|
Voiced by Amazon Polly |
As organizations accelerate cloud adoption, traditional perimeter-based security models are no longer effective. Users connect from anywhere, applications span multiple clouds, and data moves beyond corporate networks. In this reality, security must evolve, and that evolution is Azure Zero Trust Architecture.
Rather than trusting users or systems based on location, Zero Trust assumes that every access request could be a potential threat. Azure enables this strategy through tightly integrated security services that protect identity, network, and workloads without adding unnecessary complexity.
Start your career on Azure without leaving your job! Get Certified in less than a Month
- Experienced Authorized Instructor led Training
- Live Hands-on Labs
Understanding Zero Trust in the Azure Cloud
Azure Zero Trust Architecture is not a single product or configuration. It is a design philosophy built on three guiding principles:
- Verify explicitly using strong identity and contextual signals
- Apply least privilege access to reduce unnecessary exposure
- Assume breach and limit the blast radius of any attack
Azure security services are designed to support these principles natively, helping organisations implement Zero Trust as part of their overall cloud strategy rather than as an afterthought.
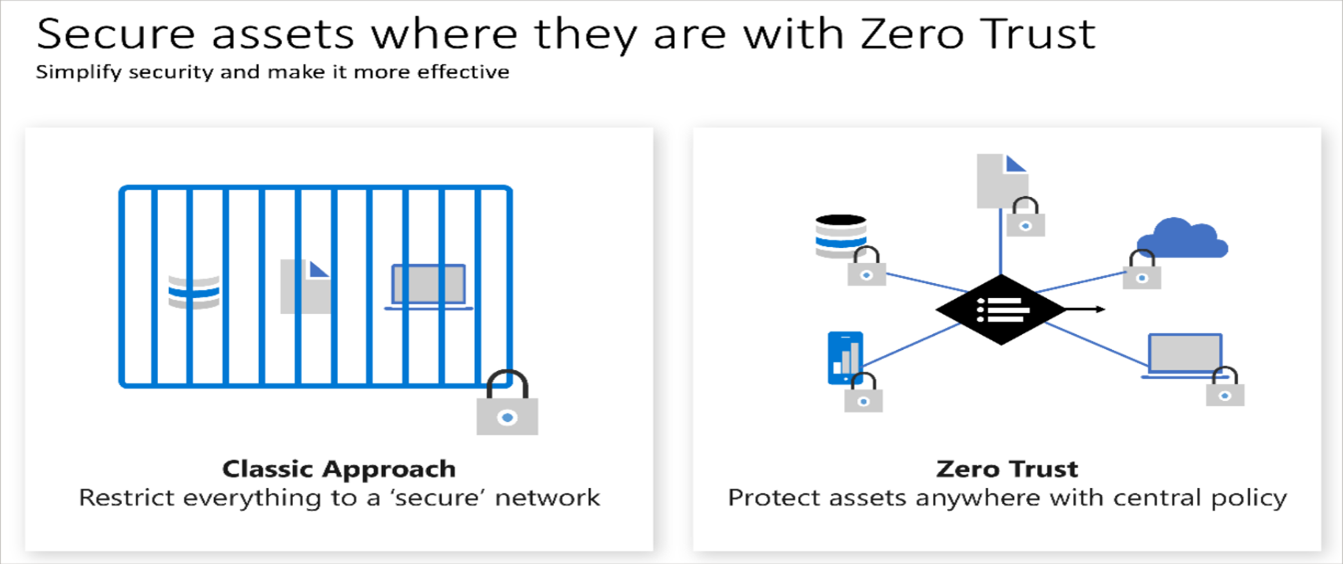
Source: Zero Trust Approach
Identity-Centric Security as the Foundation
In Zero Trust, identity becomes the primary control plane.
Microsoft Entra ID enables organizations to continuously validate users and workloads using signals such as authentication strength, risk level, and access context. Instead of granting access simply because a user is “inside the network,” access decisions are made dynamically and reassessed continuously.
This identity-first approach significantly reduces the risk posed by compromised credentials, which remain one of the most common attack vectors in cloud environments.
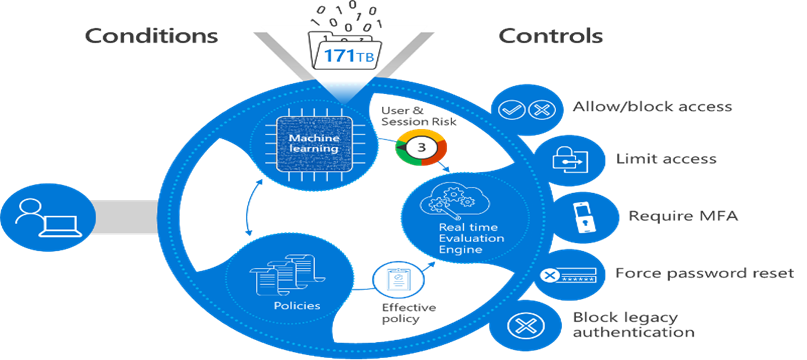
Source: Zero Trust Architecture
Network Protection Without Implicit Trust
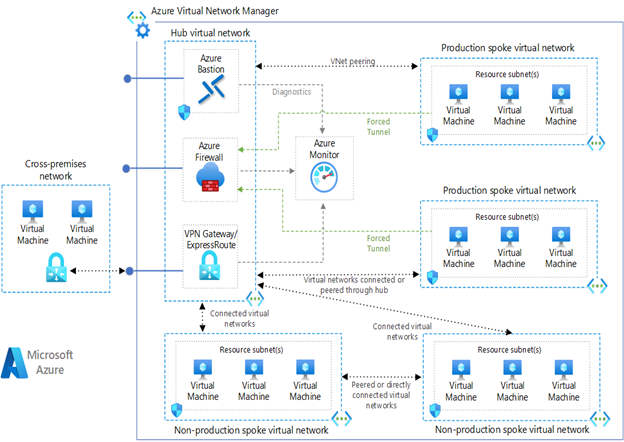
Zero Trust does not remove network security, it makes it more intentional.
Azure Firewall provides centralized traffic inspection and policy enforcement, ensuring that only explicitly allowed communication paths exist between workloads. Whether traffic originates from the internet or within Azure, it is treated with the same level of scrutiny.
By eliminating broad network trust and enforcing controlled communication, organizations can limit lateral movement and contain threats more effectively.
Continuous Security Visibility and Risk Awareness
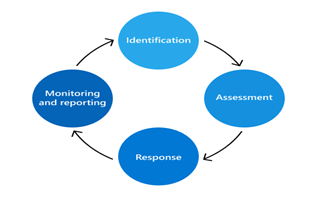
A Zero Trust strategy must be continuously validated.
Microsoft Defender for Cloud delivers ongoing visibility into security posture and risk across Azure environments. Rather than relying on periodic assessments, organizations gain continuous insight into configuration gaps, exposure risks, and potential attack paths.
This proactive visibility helps security teams prioritize remediation efforts and strengthen defenses before issues turn into incidents.
Bringing Zero Trust Together in Azure
The real value of Azure Zero Trust Architecture comes from how these components work together:
- Identity validation through Microsoft Entra ID
- Network enforcement using Azure Firewall
- Continuous posture and threat assessment with Microsoft Defender for Cloud
When combined, these capabilities form a unified security model that adapts to changing conditions while supporting business agility. Many organizations standardize this approach using enterprise-ready offerings from our
cloud security products that ensure consistent protection across environments.
Building Skills for a Zero Trust Future
Successfully adopting Zero Trust requires both the right tools and the right expertise. Security professionals must understand identity governance, network isolation, and continuous risk management to design effective architectures.
These competencies are validated through industry-recognised
Azure security certifications align closely with real-world Zero Trust design and operational scenarios.
Continuous Trust Verification
Zero Trust is no longer an optional security enhancement; it is a foundational requirement for protecting modern, cloud-native environments. By implementing Azure Zero Trust Architecture, organizations eliminate implicit Trust and adopt a security model built on continuous verification, least-privilege access, and real-time risk assessment. This approach enables adaptive, scalable, and resilient security controls that are resilient against evolving threats across identities, devices, applications, and data.
In Azure, Zero Trust is not about introducing unnecessary complexity. Rather, it is about designing security into every access decision, ensuring that authentication, authorization, and access are always intentional, context-aware, and continuously evaluated. When applied correctly, Azure Zero Trust strengthens security posture while enabling secure digital transformation in an increasingly hostile threat landscape.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Navitha Wilson
Navitha Wilson is a Microsoft Certified Trainer and Subject Matter Expert in Azure Infrastructure and Architecture at CloudThat, with a strong focus on Microsoft Azure and Hybrid Infrastructure. With over 13 years of experience in training and academics, she has empowered 5,000+ professionals and learners through her expertise in Azure Administration, Networking and Security. She is also a Cisco Certified Network Professional (CCNP) in Routing and Switching, with robust hands-on experience across cloud and on-premises environments. Renowned for her ability to simplify complex technical concepts and deliver engaging hands-on sessions, Navitha consistently receives outstanding feedback from learners and is widely recognized as an exceptional trainer. Her training style blends deep technical knowledge with practical application, ensuring impactful and results-driven learning experiences. Navitha’s passion for technology and reading fuels her unique and inspiring approach to learning and development.


 Login
Login


 March 12, 2026
March 12, 2026 PREV
PREV









Comments