|
Voiced by Amazon Polly |
In the early days of 2026, the cybersecurity landscape has undergone a tectonic shift. We are no longer just fighting malware or human-led phishing; we are defending against “Agentic AI” threats, autonomous systems capable of scanning for vulnerabilities, crafting deepfake-perfect lures, and moving laterally through networks at machine speed.
For organizations operating across Microsoft 365 (M365), on-premises, and multi-cloud environments, the defensive perimeter is no longer a firewall. It is a unified, AI-driven fabric. Here is how you can leverage the Microsoft Security stack to detect and mitigate these next-generation threats.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
1. The New Perimeter: AI-Powered Identity (Microsoft Entra)
In 2026, identity is the primary attack vector. Adversaries use AI to launch sophisticated Adversary-in-the-Middle (AiTM) attacks and bypass traditional MFA.
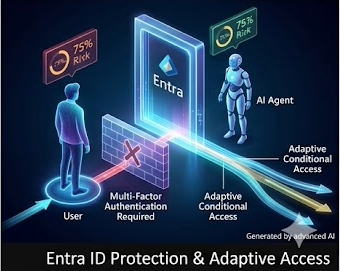
Fig 1: Adaptive access in Entra protects identities against AI‑driven attacks.
Detection: Microsoft Entra now treats AI agents as “first-class identities.” Using Entra ID Protection, the system applies behavioral analytics to detect anomalies, such as an “impossible travel” scenario in which a user (or their AI agent) logs in from two distant locations within minutes.
Mitigation:
- Adaptive Conditional Access: Moving beyond static rules, Entra now adjusts access requirements in real-time based on risk scores.
- Passkeys & Phishing-Resistant MFA: Enforcing FIDO2-compliant passkeys eliminates the risk of credential harvesting, which AI is particularly adept at scaling.
2. Detecting Lateral Movement Across Hybrid Clouds (Microsoft Defender)
The challenge in hybrid environments is the “visibility gap” between on-prem servers and cloud workloads. AI-driven threats exploit this by starting in an unpatched on-prem legacy system and jumping to M365.
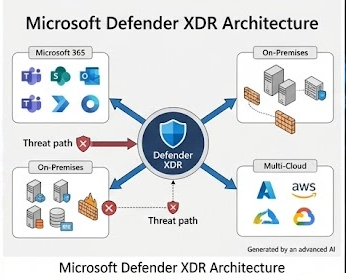
Fig 2: Unified XDR closes visibility gaps across hybrid environments.
The Solution: Unified XDR
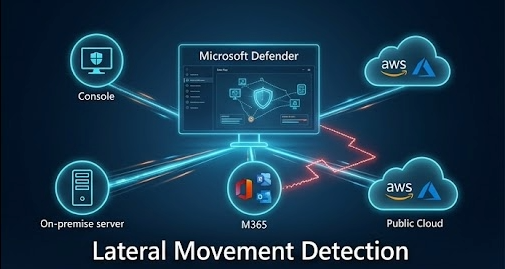
Fig 3: Unified XDR detects lateral movement across hybrid environments.
- Defender for Cloud: Uses Attack Path Analysis to visualize how an attacker could move from a vulnerable on-prem SQL server to a sensitive SharePoint site. It identifies the “weakest link” before an AI-driven bot does.
- Defender for Office 365: In 2026, this includes Suspicious Call Reporting in Teams and AI-driven analysis of collaboration apps to detect “dark patterns” in chat and file sharing that suggest an automated takeover.
3. Mastering the Data Chaos (Microsoft Purview)
AI productivity tools like Copilot are double-edged swords. If an AI agent has over-privileged access, it can accidentally surface sensitive data to the wrong user or an attacker.
Mitigation Strategies:
- AI Hub in Purview: This provides a dedicated dashboard to see how AI is interacting with your data. It blocks sensitive PII (Personally Identifiable Information) from being used as “grounding” for AI prompts.
- Just-in-Time DLP: Data Loss Prevention (DLP) policies now apply at the moment of egress. If an AI agent attempts to export a file that hasn’t been classified yet, Purview can restrict it in real-time.
4. Operationalizing Defense with Security Copilot
The most significant advancement in 2026 is the transition of Microsoft Security Copilot from an assistant to an Autonomous Agent.
Instead of a human analyst manually stitching together logs from a firewall and an email alert, Security Copilot:
- Summarizes: It instantly converts 10,000+ signals into a readable, natural-language incident report.
- Hunts: It drafts complex KQL (Kusto Query Language) queries to find if an AI-driven threat has touched other parts of the network.
- Remediates: It can automatically isolate a compromised endpoint or revoke a risky session, operating at the “speed of the attack.”
AI-Powered Security Defense
AI has become a double-edged sword in cybersecurity, empowering both attackers and defenders. In Microsoft 365, hybrid, and multi-cloud environments, organizations must adopt integrated, intelligence-driven protection. Microsoft Defender, Defender for Cloud, Defender for Identity, Defender for Endpoint, and Microsoft Sentinel together provide layered, AI-powered detection and automated mitigation. By embracing a Zero Trust approach and leveraging Microsoft’s security ecosystem holistically, security administrators can not only detect AI-driven threats early but also contain and remediate them before significant damage occurs.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Naved Ahmed Khan
Naved Ahmed Khan is a Research Associate with over 5+ years of experience in Cloud. He is an MCT and also the winner of Top 100 MCT Quality Awards Winner for 2024-25. Naved is known for adding humor into his training making it engaging and fun. He has a passion for IoT services because of his roots in Electrical & Electronics Engineering and his habit of reading fictional novels add an imaginative punch into his training method. With 12 certifications in Azure, he has trained over 1000+ individuals across different verticals like Infra & Architect, Security, Data and AI. His core skillset lies in Networking, Security, Python and Powershell.


 Login
Login


 April 29, 2026
April 29, 2026 PREV
PREV











Comments