|
Voiced by Amazon Polly |
The shift to cloud computing has fundamentally changed how organizations approach security. For enterprises in India- particularly those in financial services, healthcare, and government—this distributed landscape introduces new compliance complexities. The Digital Personal Data Protection (DPDP) Act, RBI data localization requirements, and SEBI frameworks create a compliance matrix that demands careful architectural planning.
This document explores three critical dimensions of cloud security on Microsoft Azure: implementing Zero Trust to explicitly verify every access request, navigating India’s data sovereignty requirements, and leveraging Microsoft Defender for Cloud to protect hybrid workloads. Whether planning a cloud migration or hardening current deployments, this guidance translates security principles into actionable Azure configurations.
Start your career on Azure without leaving your job! Get Certified in less than a Month
- Experienced Authorized Instructor led Training
- Live Hands-on Labs
Zero Trust Security & Data Residency Architecture
Zero Trust security inverts the traditional perimeter-based model. Instead of trusting systems inside the network, Zero Trust assumes breach at any point and requires explicit verification for every access request. Three foundational principles guide implementation: (1) verify explicitly using all available data points, (2) use least-privilege access granting minimum required permissions, and (3) assume breach by implementing detection and response capabilities.
Azure operationalizes these principles through:
- Azure Entra ID with Conditional Access enforcing context-based authentication
- Privileged Identity Management (PIM) enables time-bound administrative access
- Multi-Factor Authentication (MFA) and passwordless authentication (Windows Hello, FIDO2)
- Role-Based Access Control (RBAC) restricts permissions to specific resources
- Network Segmentation via Network Security Groups and Azure Firewall
- Continuous Monitoring through Azure Sentinel and behavioral analytics
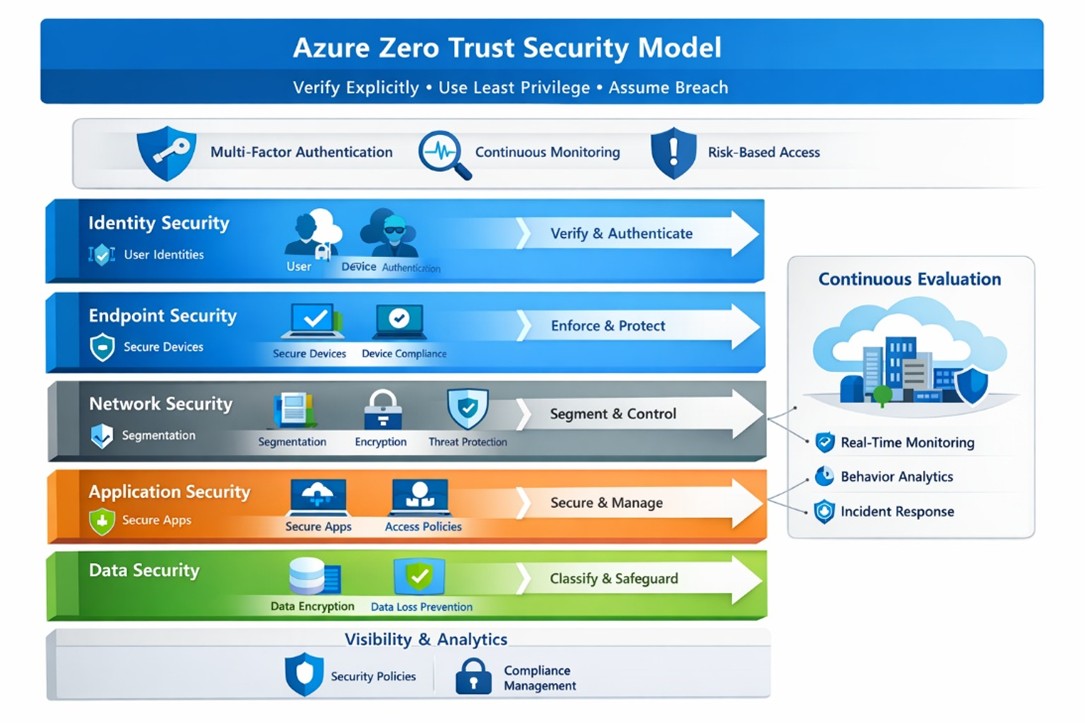
Fig 1: Zero Trust Security Model Architecture – showing three pillars (Verify Explicitly, Least Privilege Access, and Assume Breach) with Azure Entra ID, Conditional Access, PIM, and continuous monitoring components.
Data Residency for India Compliance
India’s regulatory framework- DPDP Act, RBI data localization requirements, and IRDAI rules mandate that certain data remain within national boundaries. RBI guidance requires payment and settlement data in India. DPDP applies to personal data processing. This creates a complex architecture challenge: applications are processed globally, but regulated datasets remain in-country.
Organizations should:
- Pin regulated workloads to Azure India regions (Central India – Pune, South India – Chennai)
- Implement data classification frameworks, distinguishing residency-sensitive data from operational data
- Use Azure Policy to enforce regional constraints and prevent accidental data placement outside India
- Leverage Azure Compliance Manager to verify DPDP compliance against personal data processing controls
- Maintain immutable audit logs capturing all data access patterns for regulatory audits
Azure Policy automation denies deployments that violate residency constraints, preventing configuration drift. For services with insufficient in-country processing guarantees, Azure Arc with confidential computing enables sensitive data processing on-premises while maintaining Azure management integration.
Hybrid Threat Protection & Implementation Roadmap
Microsoft Defender for Cloud provides unified threat protection across Azure resources, on-premises infrastructure (via Azure Arc), and multi-cloud platforms. A single dashboard surfaces vulnerabilities, misconfigurations, and active threats regardless of infrastructure location.
Defender’s core capabilities include:
- Posture Management: Continuous assessment against compliance standards and security baselines (CIS Benchmarks, NIST, ISO 27001)
- Threat Protection: Behavioral analytics and machine learning detect anomalous patterns indicating compromise
- Vulnerability Management: Identifying and prioritizing security issues across hybrid workloads
- Compliance Dashboard: Consolidating compliance status for DPDP, RBI requirements, and sectoral regulations
Hybrid deployment proceeds through Azure Arc onboarding. Arc-connected servers appear in the Azure portal alongside native VMs, receiving identical vulnerability scans, patch management recommendations, and threat detection. Organizations with hundreds of on-premises servers can onboard at scale using deployment scripts.
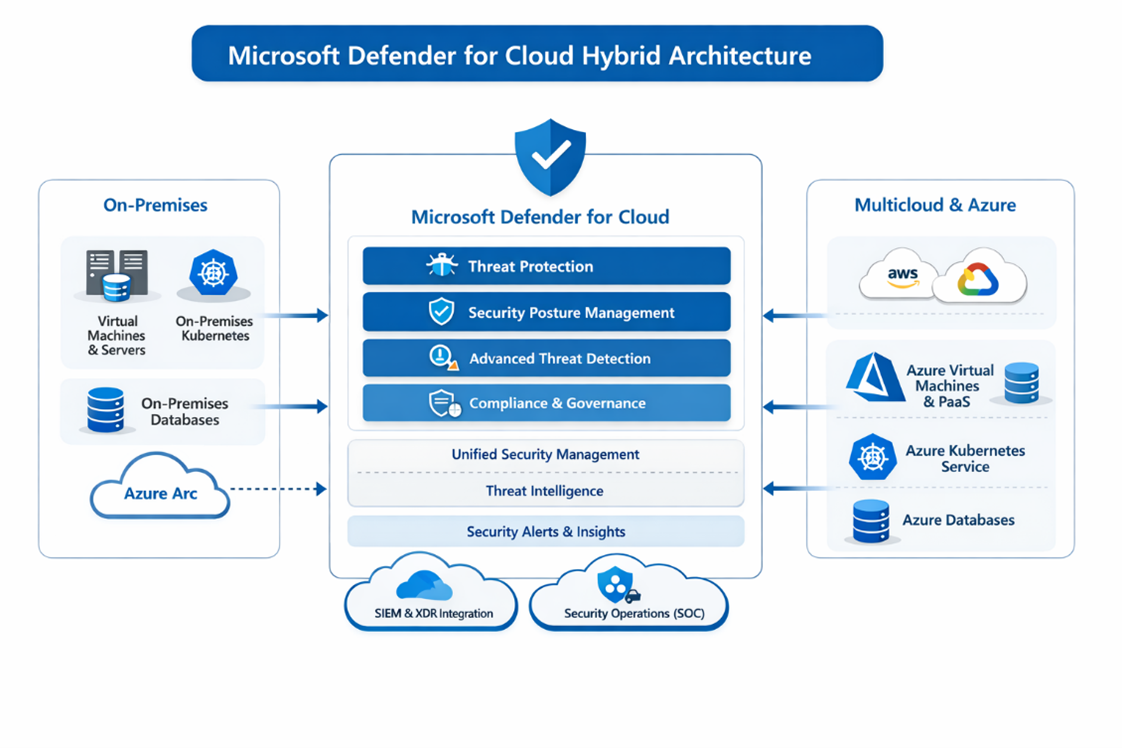
Fig 2: Microsoft Defender for Cloud Hybrid Architecture – showing unified security dashboard integrating Azure resources, on-premises servers via Azure Arc.
Azure Arc, AWS EC2, and GCP instances with centralized threat detection
Practical Implementation Roadmap
Organizations should progress through three phases:Table 1: Three-Phase Implementation Timeline
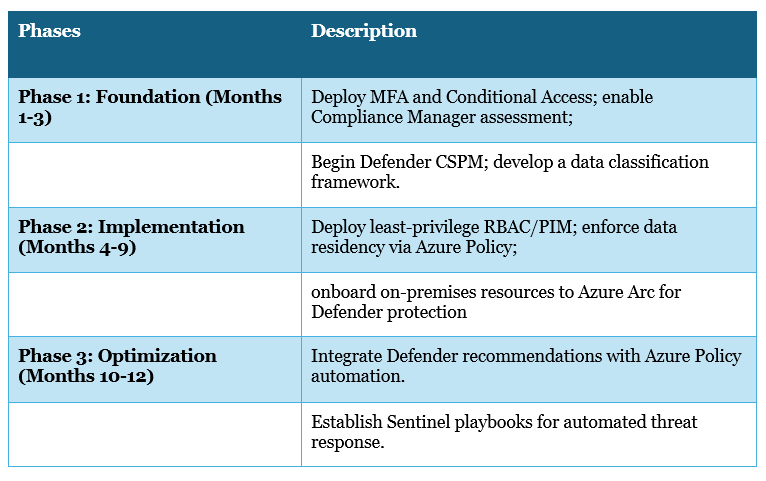
Table 1: Three-Phase Implementation Timeline
To learn and earn an Azure certification, use trusted platforms and courses such as Azure Security Solutions.
Secure Azure Governance
Cloud security for regulated Indian enterprises is no longer just a compliance checkbox—it is a strategic enabler of trust, resilience, and innovation. By adopting an integrated approach that combines Zero Trust verification, explicit data residency architecture, and unified threat protection across hybrid infrastructure, organizations can balance regulatory rigor with operational flexibility.
The measurable outcomes are clear:
- Reduced credential-based attacks through passwordless authentication.
- Accelerated threat detection powered by behavioral analytics.
- Demonstrable compliance via comprehensive audit trails.
- Operational sustainability achieved through Azure Policy and Defender automation.
This framework not only strengthens defences but also enables enterprises to scale securely without being weighed down by manual overhead. In a landscape where cyber threats evolve daily, and regulatory expectations intensify, such automation-driven security practices make resilience sustainable at enterprise scale.
Organizations implementing these practices experience measurable improvements: reduced credential-based attacks through passwordless authentication, faster threat detection through behavioral analytics, and demonstrable compliance through comprehensive audit trails. Azure Policy and Defender automation reduce ongoing operational overhead, enabling sustainable security at enterprise scale.
Access to Unlimited* Azure Trainings at the cost of 2 with Azure Mastery Pass
- Microsoft Certified Instructor
- Hands-on Labs
- EMI starting @ INR 4999*
About CloudThat

WRITTEN BY Kavya B.S
Kavya B.S is a Subject Matter Expert and MCT at CloudThat, specializing in Microsoft Azure. With 15 years of experience in training and academics, she has trained over 5,000 professionals to upskill in Architect, Administrator and Security. Known for simplifying complex concepts through real-world analogies, she brings deep technical knowledge and practical application into every learning experience. Kavya’s passion for teaching reflects in her unique approach to learning and development.


 Login
Login


 March 12, 2026
March 12, 2026 PREV
PREV











Comments