|
Voiced by Amazon Polly |
As cloud adoption grows, so do sophisticated cyber threats. Traditional perimeter-based security is no longer sufficient for modern cloud environments. Organizations need real-time threat detection to identify malicious activity within their networks.
Google Cloud Intrusion Detection System (Cloud IDS) is a managed, cloud-native service that helps detect network-based threats in GCP workloads with minimal operational overhead. In this blog, we’ll explain Cloud IDS in simple terms, how it works, key components, use cases, benefits, and best practices.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
What are Cloud IDS in GCP?
The Cloud IDS is a managed network-based intrusion detection service provided by Google Cloud. It continuously inspects network traffic to detect malware activity, command-and-control communication, exploits and suspicious behaviour. Cloud IDS is powered by Palo Alto Networks threat detection technology, bringing enterprise-grade security into GCP without requiring you to manage IDS infrastructure. Cloud IDS operates by creating a Google-managed peered network with mirrored virtual machine (VM) instances. Traffic mirrored to this peered network is inspected using Palo Alto Networks’ threat-prevention technologies to deliver advanced threat detection.
Why Cloud IDS is Needed
Cloud IDS is needed because traditional security controls like firewalls and IAM mainly prevent known access patterns but do not provide deep visibility into what is happening inside the network. In cloud environments, threats such as compromised workloads, lateral movement, malware communication, and zero-day attacks can occur even when perimeter defences are in place. Cloud IDS continuously inspects network traffic using advanced threat signatures and behavioural analysis to detect suspicious and malicious activity in real time.
Key Features of Cloud IDS
- Managed Service – No need to configure and manage sensors or appliances
- Real-Time Threat Detection – It does continuous traffic inspection
- Enterprise-Grade Signatures – Backed by Palo Alto Networks
- Native GCP Integration – Works seamlessly with VPC networks
- Centralized Logging – Alerts sent to Cloud Logging
- Scalable & Highly Available – Built on Google’s infrastructure, so you don’t need to worry about the failure of the IDS endpoint.
Getting Started with Cloud IDS
- Set up the private service access
- Create a Cloud IDS endpoint in a GCP project.
- Attach the packet mirroring policy to the Cloud IDS endpoint. Network traffic from VPCs is mirrored to the IDS endpoints.
- Traffic is analysed using threat signatures and behavioural analysis.
- Detected threats you can view in the Cloud IDS console.
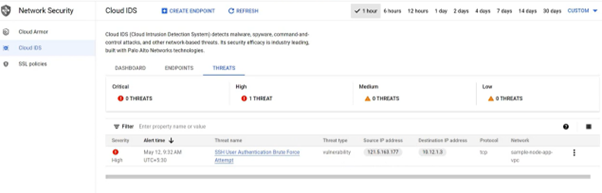
Source: Directly from the GCP console.
Cloud IDS is a passive detection service. It does not block traffic, only detects and alerts.
Use Cases of Cloud IDS
- East-West Traffic Monitoring
Cloud IDS helps detect suspicious lateral movement between workloads within the same VPC or across VPCs. Attackers often move east-west after gaining initial access, and this traffic is usually invisible to perimeter firewalls. Cloud IDS provides deep inspection of internal traffic to identify malware propagation and unauthorized access attempts early.
- Compliance & Security Monitoring
Many regulated industries require continuous monitoring and threat detection to meet compliance standards. Cloud IDS supports these requirements by providing detailed threat alerts and centralized logging. Security teams can use these logs for audits, investigations, and compliance reporting.
- Hybrid Cloud Security
In hybrid environments, traffic flows between on-premises networks and GCP through VPN or Interconnect. Cloud IDS monitors this traffic to detect threats originating from on-prem systems or targeting cloud workloads. This ensures consistent threat visibility across both on-prem and cloud environments.
- Zero Trust Architectures
Zero Trust focuses on strict access control, but visibility into network behaviour is equally important. Cloud IDS complements Zero Trust by continuously analysing traffic even after access is granted. It helps detect abnormal behaviour, compromised identities, and hidden threats within trusted network boundaries. Add visibility and detection alongside zero-trust controls.
Strengthening Cloud Security Skills in GCP
With organizations increasingly prioritizing cloud security, expertise in services such as Cloud IDS has become essential for security engineers and cloud professionals. Gaining hands-on experience through industry-aligned Google Cloud security programs helps individuals understand real-world threat detection scenarios and build confidence in securing GCP environments.
Enhanced Threat Visibility
Cloud IDS in GCP provides powerful, enterprise-grade intrusion detection with minimal management effort. While it does not block traffic, it offers critical visibility into threats that may otherwise go unnoticed. For organizations serious about cloud security, Cloud IDS is an excellent addition to a layered defence strategy.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Mahek Tamboli
Mahek is a Senior Subject Matter Expert at CloudThat, specializing in AWS Architecting. With 13 years of experience in IT and education industry, she has trained over 2000 professionals/students to upskill in hardware, network, MCSA, RHCSA and multi cloud. She is an authorized trainer for AWS and GCP. Known for simplifying complex concepts and delivering interactive and hands-on sessions, she brings deep technical knowledge and practical application into every learning experience. Mahek passion for continuous learning reflects in her unique approach to learning and development.


 Login
Login


 March 18, 2026
March 18, 2026 PREV
PREV











Comments