Security is a critical aspect for any organization. This blog focuses on the account security measure provided by AWS – IAM. IAM stands for Identity and Access Management and is used for controlling access to AWS services and resources. There are no additional charges for using IAM.
For people new to IAM, the basic concepts are:
User: A user is similar to a login user in various operating systems like Microsoft Windows. A user can log in to the AWS console using their username and password. In AWS world, this user can be an individual, system or an application requiring access to AWS resources and services.
Groups: A group is a collection of users. Instead of assigning similar permissions to multiple users individually, a group can be created with a set of permissions and users can be added to it. The benefit of creating groups is that it simplifies the tasks of managing a large number of users and their permissions.
Role: A role is a set of permissions required to make AWS service requests. But this role cannot be directly assigned to a user or group, instead roles can be assumed by a user, an application or an AWS service like EC2 to make service requests. When a user has assumed a role then their existing permissions are no longer applicable till the time they are using that role and can only perform actions specified in permissions associated with that role.
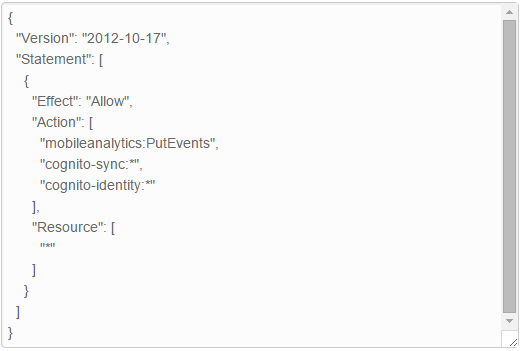
Policy: A policy is a JSON document which specifies the actions that are allowed or denied for various AWS services. A policy can be attached to a user, group or an IAM role. AWS also provides IAM policy generator and sample policies which can help in getting started with IAM policies.
IAM can be used for:
- Managing users and their access: Users and groups can be created and their access to various AWS services can be controlled.
- Manage IAM roles: The primary benefit of using an IAM role is that it provides the entity temporary access credentials to make AWS Service requests. And there is no need to give long-term credentials or define permissions for each entity that requires access to an AWS resource.
- Manage Federated users: IAM can also be used to enable identity federation which can allow on-premises users to access AWS management console, call AWS APIs and use other AWS resources without creating new IAM accounts for each entity.
We, at CloudThat, adhere to the following IAM best practices:
- Not using root account: Instead of using the root account for accessing AWS services or for calling AWS APIs, we have created IAM users with a specific set of permissions to use AWS. This is because the root account has all the permissions by default which cannot be restricted.
- Creating Individual IAM users: Instead of giving users the credentials of our root account, we have created IAM users and have given them access to only the AWS services required depending on the nature of their job.
- Using groups: Rather than assigning permissions to an individual user which can become cumbersome as the number of users increase, we have created groups having a specific set of permissions and have assigned users to those groups.We have created groups having permissions for only the services used by our clients and have added people working for that client to those groups.
- Granting least privilege: It is better to create a policy with the minimal set of permissions enabling a user to perform his tasks than creating a lenient policy and trying to tighten it later. This task surely involves a lot of work as one needs to research on what is required for a particular task, which actions are supported by a particular service and which permissions are required for performing those actions but pays off later. You can gradually add more permissions if required.
- Having a strong password policy: One of the biggest benefits of using IAM is that it is very easy to create a password policy. By going on the account settings page of the IAM console, one can create a password policy with conditions like minimum password length, type of characters which can be used and password expiry policy. One can also control if users can reuse their old passwords later or not.
Here is how our password policy looks like:
- Enabling MFA: It is important to enable MFA for users who are allowed access to sensitive resources or APIs. AWS supports both hardware and virtual MFA devices.
- Using Roles: Applications running on EC2 require credentials for accessing other AWS services, and instead of passing credentials in the user data one can use Roles to achieve this. The biggest benefit of using IAM roles is that it generates temporary credentials for access to the services and also rotates these credentials automatically.
- Delegating access through roles: Not only do roles help in making various services and applications access AWS services securely, it can also be used for enabling access of users in other accounts to resources in your account. AWS gives you the ability to control users from which accounts can access resources in your account and what are they allowed to do.
- Rotating credentials regularly: It is important to rotate credentials- passwords, access and secret keys on a regular basis. One can do this through password policy or write a custom script which can do the same.
- Using conditions in policies: Add conditions to IAM policies for fine grain control. For example: we have added conditions like which type of EC2 instances a particular user can create or if a user can terminate or stop a particular instance.
- Using CloudTrail: We use CloudTrail which logs the API calls made to an AWS account to see the actions taken by users, resources that are used along with the details like time and date of these calls, source IP and whether they were allowed to perform that action or not.
One can also use the credential report which is available from the IAM console to see the status of the credentials of all the users in your account. This can help you come up the rotation policy for passwords and access keys.
Hope this blog gave you an idea as to how you can use IAM and adhere to the best practices in order to keep your account secure. Please feel free to post questions, comments and suggestions below. 🙂
WRITTEN BY CloudThat
CloudThat is a leading provider of cloud training and consulting services, empowering individuals and organizations to leverage the full potential of cloud computing. With a commitment to delivering cutting-edge expertise, CloudThat equips professionals with the skills needed to thrive in the digital era.

Karthik
Sep 18, 2015
Very useful..!! Thank you 🙂