|
Voiced by Amazon Polly |
In today’s cloud‑first world, organizations face increasingly complex cybersecurity threats. Traditional SIEM solutions often struggle to keep up with the scale, speed, and sophistication of modern attacks. Microsoft Sentinel, a cloud‑native SIEM and SOAR platform, addresses this challenge by delivering AI‑driven threat detection, automated response, and seamless integration across hybrid environments.
Built on Azure, Microsoft Sentinel provides security teams with a unified view of alerts, incidents, and threat intelligence, reducing operational overhead and enabling faster response times.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
Microsoft Sentinel Working
Microsoft Sentinel works as a cloud-native SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) solution. The points below define a clear breakdown of how it works:
- Data Collection
Sentinel connects to various data sources like Azure services, on-premises systems, SaaS applications, and third-party tools. It uses connectors to ingest logs, events, and telemetry data from these sources.
- Data Analysis
Once data is ingested, Sentinel uses AI and machine learning to detect anomalies and suspicious activities. Correlate events across multiple sources. It applies built-in analytics rules and allows custom rule creation for threat detection.
- Threat Detection
Sentinel leverages Microsoft Threat Intelligence and other feeds to identify known attack patterns. It uses behavioural analytics to detect zero-day threats.
- Investigation
Provides a centralized dashboard for security teams to investigate alerts. Offers visual incident timelines and deep-dive capabilities to understand the attack path.
- Automated Response
Through playbooks (powered by Azure Logic Apps), Sentinel can automatically block IP addresses, disable compromised accounts, notify teams via email or Teams and reduce manual effort, speeding up incident response.
- Continuous Improvement
Sentinel supports hunting queries using KQL (Kusto Query Language) for proactive threat hunting. Security teams can refine detection rules and automation workflows over time.
Architecture
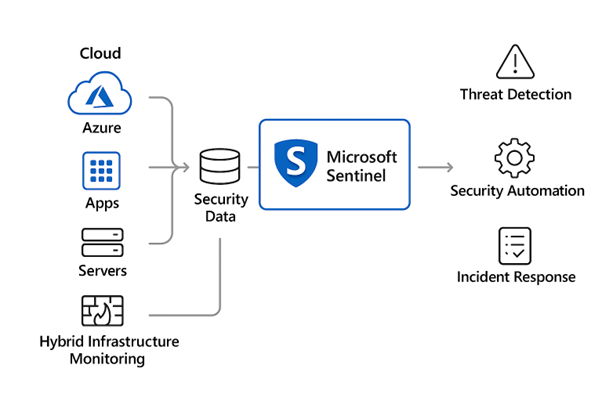
Fig1: How Microsoft Sentinel processes security data to enable threat detection, automation, and incident response.
Microsoft Sentinel Use Cases
- Threat Detection & Incident Response
Sentinel uses analytics rules, machine learning models, and threat intelligence to detect anomalies and trigger actionable incidents. SOC teams can investigate alerts using built‑in workbooks and playbooks.
- Security Automation with Playbooks
Using Azure Logic Apps, Sentinel automates repetitive tasks like alert enrichment, user suspension, IP blocking, and notification workflows, significantly reducing MTTR (Mean Time to Respond).
- Cloud & Hybrid Infrastructure Monitoring
Sentinel centralizes logs from Azure, AWS, GCP, on‑premises servers, firewalls, and network appliances, ensuring complete visibility and compliance across diverse environments.
- Insider Threat Detection
With UEBA (User and Entity Behaviour Analytics), Sentinel identifies unusual behaviour, such as privilege misuse, abnormal file access, or lateral movement, which are critical for preventing insider‑driven breaches.
- Compliance & Audit Readiness
Sentinel provides pre‑built compliance dashboards (PCI, CIS, ISO, SOC) and maintains audit logs, making regulatory reporting and governance significantly easier.
Real‑Time Scenarios Where Microsoft Sentinel Excels
Scenario 1: Ransomware Attack Detection
A suspicious PowerShell script attempts to encrypt files on multiple servers. Sentinel detects unusual file activity, correlates it with a known ransomware signature, triggers an incident, and automatically isolates the endpoint, blocks the malicious IP and notifies the SOC team.
Scenario 2: Compromised User Account
A user logs in from an unusual country while also appearing active locally. UEBA flags impossible travel behaviour. Sentinel creates a high‑severity incident, forces MFA re‑authentication, and disables the account until reviewed.
Scenario 3: Suspicious Firewall Activity
Sentinel receives logs showing thousands of failed inbound connections on Port 22. It identifies a brute‑force pattern, enriches the alert with threat‑intel data, and auto‑blocks the attacking IP range.
Scenario 4: Data Exfiltration Attempt
Large volumes of data are transferred outbound from a critical database server. Sentinel correlates network logs, detects an anomaly, triggers an alert, and immediately sends firewall rule updates notifications to the security engineer.
Scenario 5: Malware Spread in Internal Network
A workstation begins scanning multiple internal hosts, indicating potential worm activity. Sentinel correlates the behaviour, sends commands to isolate affected machines, and initiates malware scanning scripts
AI-Driven Security Operations
Microsoft Sentinel stands out as a powerful, cloud-native SIEM and SOAR solution that empowers organizations to proactively detect, investigate, and respond to security threats. Its scalability, AI-driven analytics, and seamless integration with Microsoft and third-party tools make it an ideal choice for modern enterprises seeking robust security posture management. By leveraging automation and advanced threat intelligence, Sentinel not only reduces alert fatigue but also accelerates incident response, enabling security teams to focus on strategic initiatives. In an era of evolving cyber threats, adopting Microsoft Sentinel is a forward-thinking step toward building a resilient and adaptive security framework.
Master Microsoft Security Training: Enhance Your Cyber Defense Skills
- Hands-on Experience
- Certification Prep
- Advanced Threat Detection
About CloudThat

WRITTEN BY Mahendra Patel
Mahendra Patel is Subject Matter Expert in Azure Infra/Arch at CloudThat, with a passion for empowering professionals through top-tier Microsoft training. As an MCT he brings over 13 years of rich experience in training, academics and research. He holds 18+ professional certifications across Microsoft ecosystem and has successfully trained over 2200+ professionals in Azure Solution Architect, Azure Administrator, Azure Network, PowerBI, Azure Security and AI Data Engineering. His hands-on, tool-driven approach to training is known for translating complex concepts into practical, real-world solutions.


 Login
Login


 March 11, 2026
March 11, 2026 PREV
PREV









Comments