|
Voiced by Amazon Polly |
Introduction
Building a SaaS product sounds straightforward until you onboard your fiftieth tenant and realize your architecture was never designed to handle the tension between isolation, cost, and scale. Early stage teams typically start with one of two extremes: a fully shared stack where every customer’s data sits in the same tables with application-level filtering, or a fully dedicated stack where each customer gets their own infrastructure. Both approaches collapse under pressure.
The shared model fails when a compliance audit demands proof that Tenant A’s data is physically inaccessible to Tenant B, and all you can offer is a WHERE clause. The dedicated model fails when your Operations team is manually managing 300 CloudFormation stacks, and every security patch takes a week to roll out. The cost curve diverges too: shared infrastructure keeps margins healthy but introduces risk, while dedicated infrastructure satisfies auditors but erodes profitability on smaller accounts.
The architecture challenge is not picking one model. It is about designing a platform that supports multiple isolation postures simultaneously, allowing you to place each tenant at the right point on the isolation spectrum based on their contract, compliance requirements, and willingness to pay. That requires deliberate decisions at every layer – identity, compute, storage, and operations.
Pioneers in Cloud Consulting & Migration Services
- Reduced infrastructural costs
- Accelerated application deployment
Architecture Overview
A well-designed multi-tenant SaaS platform on AWS separates into two distinct planes. The control plane handles tenant lifecycle management: onboarding, configuration, billing, metering, and tier assignment. This plane is always shared, there is no value in duplicating tenant management infrastructure. The data plane handles the actual application workloads that tenants interact with, and it is here that isolation decisions are implemented.
The critical architectural principle is tenant context propagation. A tenant identifier must be established at authentication, embedded in the security token, validated at the API boundary, extracted by compute services, and enforced at the data layer. This is not simply passing a header through a call chain. It means that at every boundary, Amazon API Gateway, AWS Lambda, Amazon DynamoDB, and Amazon S3, there is an independent enforcement mechanism that prevents cross-tenant access even if upstream logic fails. The system must be designed so that a bug in your application code cannot result in one tenant reading another tenant’s data, because AWS IAM policies and resource-level controls act as independent guardrails.
Architecture Diagram

The user authenticates against Amazon Cognito, which issues a JWT containing a tenant_id custom claim. This token reaches Amazon API Gateway, which validates the signature and checks expiration. Amazon API Gateway also applies usage plans keyed to the tenant, enforcing request-per-second limits, this is the first layer of noisy neighbor protection.
The validated request reaches the compute layer. AWS Lambda function or Amazon ECS task extracts tenant_id from the authorizer context, never from user-supplied input. Before making any downstream call, the compute
layer assumes a scoped AWS IAM role using STS AssumeRole with session tags. The resulting temporary credentials include conditions that restrict Amazon DynamoDB access to items whose partition key matches the tenant, Amazon S3 access to objects under the tenant’s prefix, and Amazon Aurora access to the tenant’s schema. This means the credentials themselves are incapable of touching another tenant’s resources, regardless of what the application code attempts.
Every log entry, Amazon CloudWatch metric, and X-Ray trace includes tenant_id as a dimension, enabling per-tenant observability without additional tooling.
Tenant Isolation Models
Shared (Pooled) Model:
Every tenant shares compute, tables, and buckets. Amazon DynamoDB uses tenant_id as the partition key. Amazon S3 uses prefix-based separation. Lambda functions serve all tenants.
This model suits high-volume, low-touch SaaS, such as a task management tool with 10,000 free-tier teams. The economics are compelling: infrastructure costs are amortized, deployments are single, and onboarding is instant. The risk is real, though. A missing tenant filter in a query exposes cross-tenant data. A single tenant running a bulk export can consume all provisioned Amazon DynamoDB capacity. You need per-tenant throttling, AWS IAM session policies as a safety net, and rigorous code-review discipline for data access patterns.
Silo (Dedicated) Model:
Each tenant receives dedicated resources, separate Amazon Aurora instances, dedicated Amazon ECS services, and potentially separate AWS accounts managed through AWS Organizations.
This is the model for regulated industries. A healthcare analytics company serving hospital networks needs to demonstrate to auditors that Patient data from Hospital A is physically stored in a different database than Hospital B. Silo delivers that proof trivially. The cost is significant: you are managing N independent deployments. Every schema migration, every dependency update, every configuration change must be orchestrated across all tenant stacks. AWS CodePipeline with per-tenant stages and AWS CloudFormation StackSets helps, but the operational surface area is fundamentally larger.
Hybrid (Bridge) Model:
Most mature SaaS platforms land here. Free and standard tenants share the pooled infrastructure. Enterprise and regulated tenants get dedicated resources. A tenant metadata service, a simple Amazon DynamoDB table mapping tenant_id to tier, region, and resource endpoints – drives routing decisions. When a tenant upgrades, AWS Step Functions workflow provisions dedicated resources and migrates their data.
A fintech platform might run retail users on shared AWS Lambda and Amazon DynamoDB while provisioning each banking partner a dedicated Amazon Aurora cluster and Amazon ECS service. The complexity lives in the routing and provisioning layer, but the flexibility justifies it.
Decision Framework
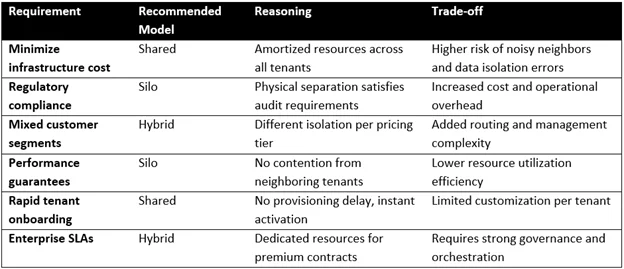
The hybrid model is not a compromise – it is a deliberate architecture that maps business tiers to infrastructure tiers. The decision is not purely technical. Contract terms, compliance obligations, and margin targets drive it. A tenant paying $50/month cannot justify a dedicated Amazon Aurora instance. A tenant paying $50,000/month cannot accept shared Amazon DynamoDB throughput with no performance guarantees.
AWS Services and Why?
Amazon API Gateway provides the first enforcement boundary. Usage plans enforce per-tenant rate limits before compute is invoked, preventing a single tenant from overwhelming backend services.
AWS Lambda suits bursty, short-lived tenant workloads. Reserved concurrency per function prevents one tenant’s traffic spike from starving others. ECS is the choice for long-running processes, persistent connections, or workloads requiring custom runtimes – silo tenants often get dedicated Amazon ECS services.
Amazon DynamoDB’s partition key design is the primary isolation mechanism in pooled models. On-demand capacity mode absorbs unpredictable per-tenant traffic without manual scaling.
Amazon S3 prefix-based partitioning, combined with Access Points or session-scoped AWS IAM policies, provides clean per-tenant boundaries. Lifecycle rules can be scoped per prefix for tenant-specific data retention.
Amazon Aurora with schema-per-tenant balances isolation strength against operational overhead. Row-level security policies add database-enforced protection independent of application logic.
Amazon Cognito handles authentication and embeds tenant context into tokens, keeping identity management out of your application code.
AWS IAM with session tags and ABAC generates dynamically scoped credentials, the most critical enforcement layer in the entire architecture.
Design Decisions
Tenant identity must originate from the identity provider, not from application logic. Amazon Cognito embeds the tenant_id as a custom claim during authentication. Every downstream service reads this claim from the validated token context. If you allow tenant identity to be derived from request parameters or URL paths, you create an attack surface that allows a malformed request to impersonate another tenant.
Data partitioning strategy depends on scale. A single-table design in Amazon DynamoDB with tenant_id as the partition key works for most pooled scenarios. Avoid creating a table per tenant, AWS account-level table limits, and the operational burden of managing thousands of tables make this approach collapse beyond a few hundred tenants. In Amazon Aurora, schema-per-tenant provides meaningful isolation without the cost of instance-per-tenant. For Amazon S3, prefix-based separation is sufficient when combined with AWS IAM enforcement.
Scaling must be tenant-aware. AWS Lambda concurrency limits should be set per function to prevent monopolization. Amazon ECS auto-scaling should track per-tenant metrics, not just aggregate CPU. Amazon DynamoDB on-demand mode eliminates capacity planning but requires monitoring per-tenant consumption to detect abuse.
Stateless compute is non-negotiable. Session state should be stored in Amazon DynamoDB or Amazon ElastiCache, scoped by tenant_id. Stateless services are easier to scale horizontally, can be replaced during failures, and can be isolated per tenant.
Trade-offs
Cost versus isolation is the defining tension. Silo deployments cost three to five times as much per tenant as pooled deployments, depending on the services involved. For a tenant paying $29/month, dedicated Amazon Aurora is economically impossible. For a tenant subject to HIPAA obligations, sharing Amazon DynamoDB with application-level filtering is legally insufficient. The hybrid model exists precisely to resolve this tension, but it introduces its own costs in terms of routing complexity and dual operational models.
Performance versus complexity is the second axis. In a pooled model, you must build throttling, queuing, and per-tenant monitoring to prevent degradation. That infrastructure has its own failure modes. A misconfigured usage plan can throttle a legitimate tenant. An under-provisioned Amazon DynamoDB table can create latency spikes that affect all tenants simultaneously. Silo eliminates these concerns per tenant, but multiplies them across your fleet.
Operational overhead compounds with silo count. Two hundred silo tenants means two hundred deployments for every patch. A failed migration in one tenant stack should not block others, which requires independent rollback capabilities and deployment orchestration.
When Not to Use Multi-Tenancy?
Multi-tenancy adds architectural complexity that is only justified at scale. If you are building an internal tool for a single organization, the tenant abstraction adds cost with zero benefit. If your total market is fifteen enterprise clients who each expect deep customization, you are better served by a single-tenant deployment model with per-client configuration – the multi-tenant routing and isolation layers would add complexity without meaningful resource sharing. If every customer requires identical, strict isolation regardless of tier, you are effectively building single-tenant software that is repeatedly deployed, and the pooled infrastructure layer provides no value.
Real-World Challenges
Noisy neighbors are the most common production issue in pooled architectures. A single tenant running a data export can consume all available AWS Lambda concurrency or Amazon DynamoDB read capacity, degrading every other tenant. Mitigation requires per-tenant concurrency limits on AWS Lambda, usage plans on Amazon API Gateway, and Amazon DynamoDB on-demand mode with Amazon CloudWatch alarms on per-tenant consumption metrics.
Data leakage rarely comes from security breaches. It comes from application bugs, a missing tenant filter in a database query, an unscoped S3 ListObjects call, or a logging statement that includes another tenant’s data. AWS IAM session policies are the critical safety net: even when application logic fails, the credentials themselves cannot access resources outside the active tenant’s scope.
Scaling bottlenecks appear at service quota boundaries. Amazon Cognito has per-user, per-pool rate limits for authentication. Amazon API Gateway has account-level throttle limits. AWS Lambda has regional concurrency limits. These quotas must be monitored and proactively increased before they become production incidents.
Governance complexity increases when tenants span regions for data residency. Your control plane must track which region each tenant’s data resides in and route requests accordingly, adding a geographic dimension to every routing decision.
Cost Considerations
Storage costs in Amazon S3 are low per tenant but compound with versioning, cross-region replication, and lifecycle policies. Amazon DynamoDB costs are driven by read/write throughput and storage, and a single-table design minimizes global secondary index overhead compared to table-per-tenant approaches.
Compute costs differ by model. AWS Lambda charges per invocation and duration; pooled models amortize cold starts across tenants, while silo deployments mean each tenant absorbs their own. Amazon ECS costs are driven by task count and size – right-sizing containers per tenant tier prevents over-provisioning.
The hybrid model’s routing, provisioning automation, and dual monitoring infrastructure add roughly fifteen to twenty percent engineering overhead compared to pure pooling. From a FinOps perspective, AWS Cost Allocation Tags on all tenant resources and application-level metering of per-tenant consumption are essential for accurate margin analysis and pricing decisions.
Conclusion
Start with the pooled model. It delivers the fastest time to market, the lowest operational overhead, and sufficient isolation for most early-stage products – provided you invest immediately in tenant-aware IAM policies, per-tenant throttling, and structured logging with tenant_id dimensions.
Introduce silo tiers when enterprise contracts or regulatory requirements demand physical separation. Design the hybrid routing layer early, even if you initially use only the pooled path, and retrofit tenant-aware routing into a system that assumes a single deployment model is significantly more expensive than building the abstraction from the start.
The evolution path for most successful SaaS platforms follows a clear trajectory: pooled at launch, hybrid as the customer base diversifies, with a silo reserved for tenants whose compliance or performance requirements justify the cost. The key is making tenant isolation a first-class architectural concern from day one, embedded in your data model, AWS IAM policies, observability stack, and deployment pipeline, so that moving along this spectrum is an operational decision, not a re-architecture.
Additional Technical Insights
In large-scale SaaS environments, the choice between data stores is driven by access patterns and scalability requirements rather than preference alone. Amazon DynamoDB is typically well-suited for pooled (shared) multi-tenant models because it provides predictable performance through partition-based scaling and simplifies tenant isolation using a tenant identifier as part of the primary key. In contrast, Amazon Aurora or other relational databases become more appropriate when the application requires complex relationships, joins, or transactional integrity that cannot be efficiently modeled in a NoSQL structure.
From an operational perspective, tenant behavior often evolves. In production systems, it is common to observe that a small number of tenants generate a disproportionately high share of traffic. When a tenant begins contributing a significant portion of total system load (for example, around 20% or more), it becomes a strong candidate for migration from a shared model to a hybrid or fully isolated (silo) model. This transition helps maintain performance stability for other tenants while enabling dedicated scaling and resource allocation for high-demand customers.
Drop a query if you have any questions regarding SaaS Multi-Tenant Architecture and we will get back to you quickly.
Making IT Networks Enterprise-ready – Cloud Management Services
- Accelerated cloud migration
- End-to-end view of the cloud environment
About CloudThat

WRITTEN BY Sana Pathan
Sana Pathan is the Head of Infra, Security & Migrations at CloudThat and also leads the Managed Services and FinOps verticals. She holds 7x AWS and Azure certifications, spanning professional and specialty levels, demonstrating deep expertise across multiple cloud domains. With extensive experience delivering solutions for customers in diverse industries, Sana has been instrumental in driving successful cloud migrations, implementing advanced security frameworks, and optimizing cloud costs through FinOps practices. By combining technical excellence with transparent communication and a customer-centric approach, she ensures organizations achieve secure, efficient, and cost-effective cloud adoption and operations.


 Login
Login


 April 10, 2026
April 10, 2026 PREV
PREV










Comments