|
Voiced by Amazon Polly |
Overview
This blog post provides a comprehensive operational guide for administering Palo Alto Networks security infrastructure, specifically focusing on Panorama, VM-Series, and CN-Series firewalls.
This guide is structured to help security and network administrators perform day-to-day operations with clarity and consistency.
Pioneers in Cloud Consulting & Migration Services
- Reduced infrastructural costs
- Accelerated application deployment
Introduction
This document aims to provide a step-by-step SOP (Standard Operating Procedure) for managing Palo Alto security components.
Access Management
How to Access Panorama and Firewalls
- Via Web UI or CLI using a secure bastion/jump host
- Ensure only authorized users have access to the firewalls or Panorama
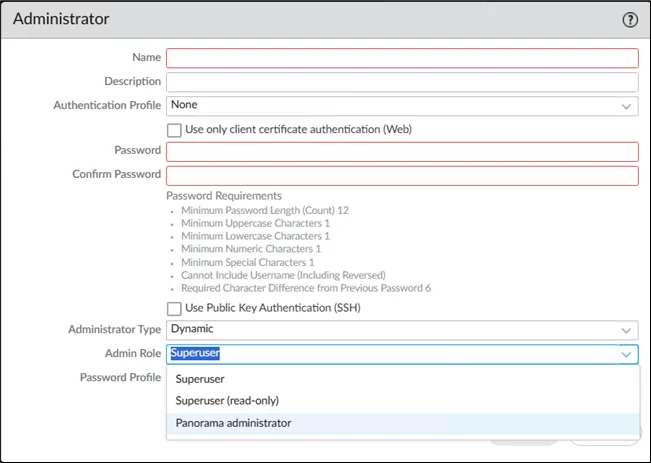
Adding New Administrator Users
- Go to Panorama, then Administrators, then Add
- Enter username, password, and select role
- Set the Administrator Type to Dynamic
- Use the appropriate password profile
Firewall Management
Adding a New Firewall to Panorama
In the event of a firewall failure or provisioning a new VM-Series instance, follow these steps:
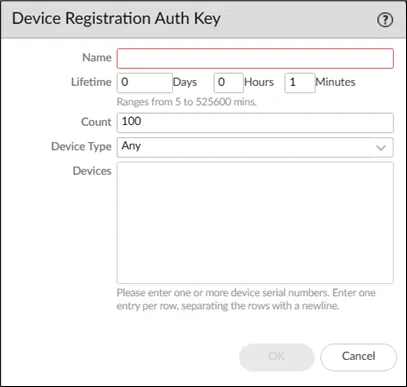
Generate Device Registration Auth Key
- Navigate to Panorama > Device Registration Auth Key
Include a key that contains the name, type, count, and lifetime.
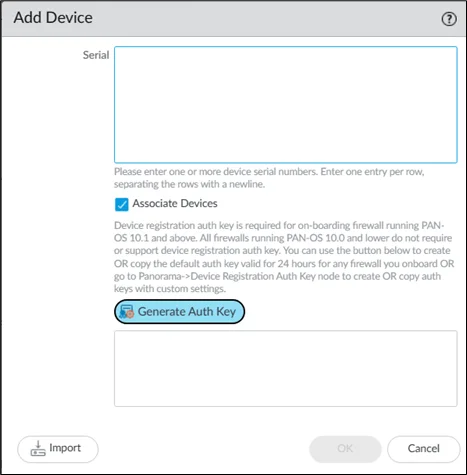
Add the New Firewall
- Go to Panorama > Managed Devices > Summary → Add
- Paste the Authentication Key after entering the serial number.
- Associate:
- Appropriate Device Group
- Template (based on Availability Zone)
- Log Collector
4. Enable Auto Push on First Connect
Configure Panorama on Firewall
- Go to Firewall UI → Device > Setup > Management
- Input Panorama IP and Auth Key
- Commit changes on both the firewall and Panorama
- Verify device status shows Connected
Associate GWLB Endpoints (If Applicable)
Use the CLI:
|
1 |
request plugins vm_series aws gwlb associate vpc-endpoint <vpce-id> interface ethernet1/1.1 |
Check with:
|
1 |
show plugins vm_series aws gwlb |
Firewall Policy Management
Adding or Modifying Security Rules
- To access Pre Rules, select Policies > Security.
- Select Device Group (based on environment)
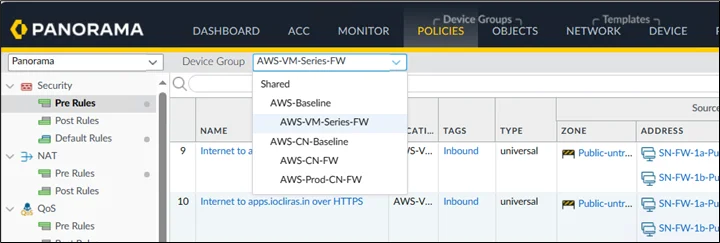
3. Define:
-
- Rule Name, Source/Destination
- Applications, Services
- Actions (Allow/Deny), Log Forwarding
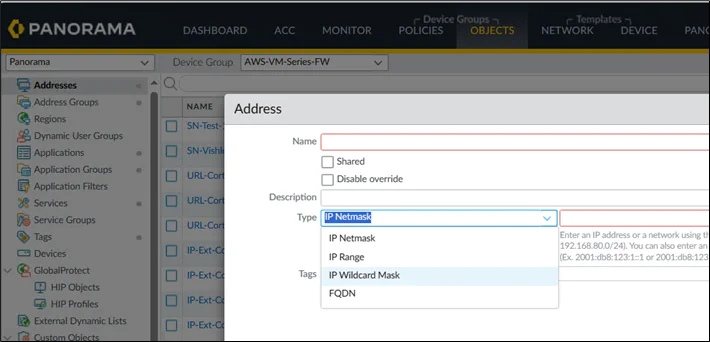
Firewall Object Management
Types of Objects You Can Create
- Address Object: Static IP or FQDN
- Static Address Group: Collection of addresses
- Dynamic Address Group: Use match criteria (tags)
- Service Object: Custom TCP/UDP ports
- Custom URL Category: For specific domain filtering
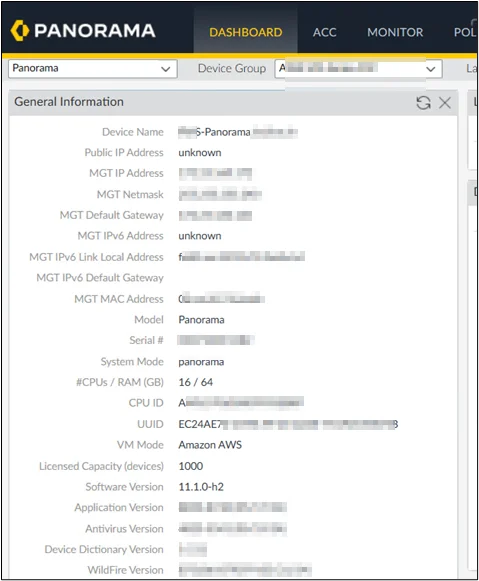
Software and Content Updates
- Backup Panorama config:
Setup > Operations > Save/Export - Update all dynamic packages (AV, Threats, WildFire, URL)
- To access Pre Rules, click Policies, then Security
- Download, Install, and Reboot (if prompted)
- Validate software version on Dashboard
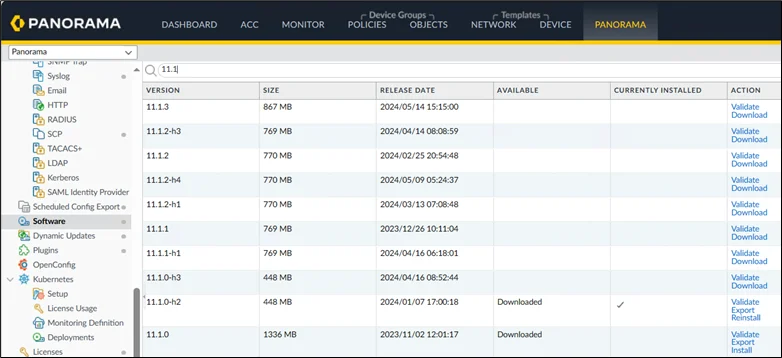
VM-Series Firewall Software Upgrade
- Export config backup:
Setup > Operations > Export Config Bundle - Update Dynamic Content:
Device Deployment > Dynamic Updates - Upgrade PAN-OS via:
Device Deployment > Software > Install - Reboot the firewall after installation
- Repeat for all AZ firewall instances
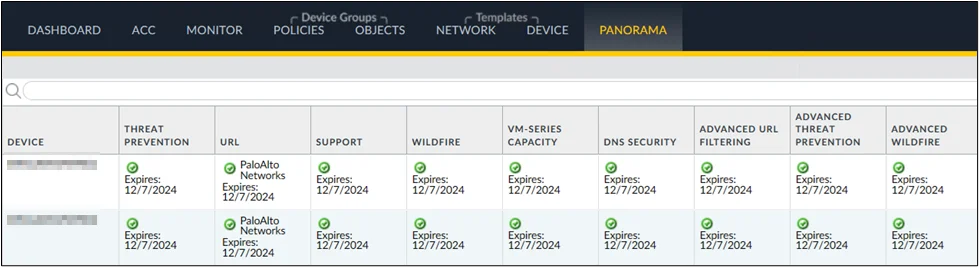
License Management
Refresh Existing Licenses
- Go to Device Deployment > Licenses > Refresh
Activate New Licenses
- Go to Device Deployment, then click on Licenses > Activate
- Input Auth Code → Click Activate
Some support licenses may need to be activated directly from the firewall interface.
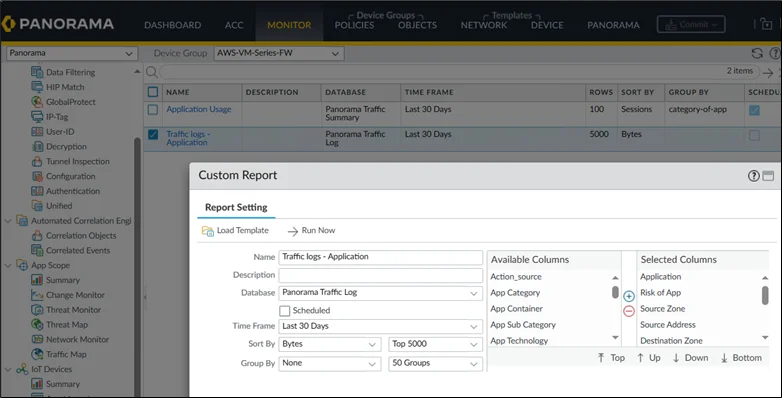
Custom Reports
- Go to Manage Custom Reports
- Add or edit reports with required filters
- To generate click run and download reports
Conclusion
This guide offers an actionable reference for the day-to-day operations of Palo Alto Networks’ security infrastructure. Admins can ensure secure, up-to-date, and resilient firewall management using Panorama by following these structured procedures.
Drop a query if you have any questions regarding Palo Alto Networks’ and we will get back to you quickly.
Empowering organizations to become ‘data driven’ enterprises with our Cloud experts.
- Reduced infrastructure costs
- Timely data-driven decisions
About CloudThat
FAQs
1. Do I need to reboot after every software update?
ANS: – Only if prompted. Panorama and firewalls may or may not require a reboot depending on the update version.
2. Can I rollback a firewall upgrade?
ANS: – Yes, if a config snapshot and the previous version are available. Always take a backup before upgrading.
3. Can I commit rules on Panorama without pushing them immediately?
ANS: – Yes, use Commit to Panorama and push later using Push to Devices.

WRITTEN BY Noopur Shrivastava
Noopur Shrivastava works as a Research Associate at CloudThat, where she is deeply passionate about cloud computing technologies such as AWS and Azure. She continuously strives to expand her knowledge and gain practical industry experience. As an effective communicator and strong team player, she is always eager to embrace new challenges and grow in her role. Her enthusiasm for learning and exploring emerging technologies, combined with her technical skills, enables her to contribute meaningfully to any team within the cloud domain.


 Login
Login


 August 29, 2025
August 29, 2025 PREV
PREV











Comments