|
Voiced by Amazon Polly |
Microsoft 365 Copilot is revolutionizing productivity by integrating generative AI into daily workflows. As organizations embrace Copilot, safeguarding sensitive data becomes paramount. Microsoft Purview, with its suite of data governance and compliance tools, plays a crucial role in managing Copilot’s data security. This blog explores how Purview, augmented by Artificial Intelligence (AI) and Data Security Posture Management (DSPM), provides robust security for M365 Copilot. IT trainers and security professionals will find practical insights into leveraging Purview products, integrating AI and DSPM, and adopting Copilot securely.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
Understanding Data Security in M365 Copilot: Importance and Challenges
M365 Copilot leverages organizational data to generate insights and automate processes. This power comes with unique security challenges:
- Data Exposure: Copilot accesses emails, documents, and chats, increasing the risk of unauthorized data exposure.
- Compliance Risks: Generative AI may inadvertently surface sensitive or regulated information.
- Data Governance Complexity: Managing access, retention, and compliance across diverse data sources is challenging.
Ensuring data security in Copilot is essential for protecting intellectual property, maintaining compliance, and building user trust.
Role of Purview in Managing Copilot Security: Key Products and Features
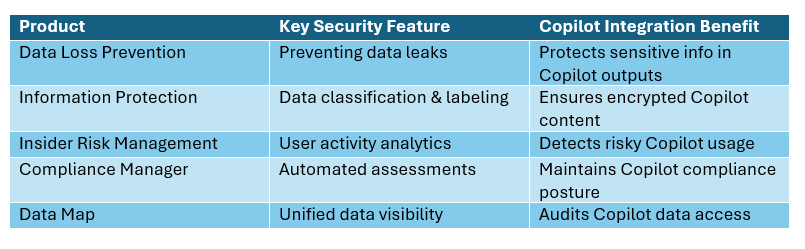
Microsoft Purview provides a comprehensive platform for managing M365 Copilot security. Key Purview products and features include:
- Purview Data Loss Prevention (DLP): Monitors and restricts sensitive data sharing across M365 apps, including Copilot-driven interactions.
- Purview Information Protection: Classifies and labels sensitive data, applying encryption and access controls to Copilot-accessed content.
- Purview Insider Risk Management: Detects and mitigates insider threats by analyzing user behaviors in Copilot-generated actions.
- Purview Compliance Manager: Provides real-time compliance scorecards and automated assessments for Copilot usage.
- Purview Data Map: Offers a unified view of organizational data, enhancing visibility into what Copilot can access and process.
By configuring Purview policies, administrators can enforce granular controls over Copilot’s data access, sharing, and retention.
Integrating AI and DSPM for Enhanced Security
AI in Purview enhances threat detection, automates policy enforcement, and identifies anomalous Copilot behaviors. Data Security Posture Management (DSPM) provides continuous risk assessment and remediation workflows for data accessed by Copilot. Key integrations include:
- Automated Classification: AI-driven engines automatically classify new data generated or accessed by Copilot, ensuring up-to-date protection.
- Anomaly Detection: Machine learning models detect unusual Copilot queries or data access patterns, alerting administrators to potential breaches.
- DSPM Dashboards: Visualize data security posture across Copilot activities, enabling rapid response to emerging risks.
- Remediation Automation: AI and DSPM jointly recommend and execute remediation actions for Copilot-related security incidents.
By combining Purview’s governance with AI and DSPM, organizations achieve proactive, scalable data security for M365 Copilot deployments.
Best Practices for Managing Copilot Security in Purview
To maximize Copilot security in Purview, IT trainers and security professionals should:
- Define Access Policies: Use Purview to set explicit access controls for Copilot, limiting exposure to sensitive data.
- Monitor Copilot Activities: Leverage Purview’s analytics to track Copilot interactions and flag suspicious behaviors.
- Regularly Update DLP Rules: Adapt Data Loss Prevention policies as Copilot evolves and new data types emerge.
- Train Users: Educate staff on responsible Copilot usage and Purview’s security features.
- Review Compliance Reports: Routinely audit Copilot-related compliance assessments in Purview.
These practices help organizations maintain a strong data security posture while unlocking Copilot’s productivity benefits.
Securing Copilot with Purview
Securing M365 Copilot requires advanced data governance and real-time threat mitigation. Microsoft Purview, enhanced by AI and DSPM, equips organizations to protect sensitive information, comply with regulations, and maintain user trust. By following best practices and submission guidelines, trainers and security professionals can share authentic, technically accurate insights that help their peers navigate the evolving Copilot security landscape.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Foram Shah
Foram Shah is a Microsoft Certified Trainer and Technical Lead in Cloud Security & BI at CloudThat. With 8+ years of experience, she specializes in full-time training on XDR, Defender, Sentinel, Microsoft Purview, M365 Copilot, Security Copilot, and broader cybersecurity topics. She has trained over 1000 professionals from top organizations including Wipro, Infosys, TCS, Accenture, Flipkart, and Microsoft partners. Her expertise lies in delivering customized, hands-on training aligned with business needs and enterprise security goals.


 Login
Login


 March 6, 2026
March 6, 2026 PREV
PREV











Comments