|
Voiced by Amazon Polly |
Understanding Public and Private Internet
What is a public network? A public network is an unrestricted network accessible to anyone with a device having access to the internet, or we can say which can be accessed over the internet.
What is a private network? A private network is a network that uses personal space and can only be accessed by people who have special permission to access it, such as a password-only password manager or security software for a public Wi-Fi hotspot.
Both come with some pros and cons. A private network is more complicated to set up and also time-consuming, but it is more secure. On the other hand, a public network is easily accessible. Still, it is less secure than a private network because the data transmitted over such an open link is frequently not encrypted. It attracts hackers’ attention.
As we talk about networks, it is also essential to talk about IP addresses.
IP addresses can locate a specific device or computer over a public or private network. Imagine a city with houses and buildings connected by roads and highways. How do you recognize your relative’s house? The answer is through an address, the same way in IT to recognize any device over a network, there is an address for every device known as an IP address.
Just like there are Public and Private networks, there are Public and Private IP addresses.
Your Internet Service Provider (ISP) assigns your router a public (or external) IP address. You can use it to connect to the internet inside and outside your network. It is like an address plate outside your house or a building in a city. This address can be traced back to your ISP.
Your network router assigns your device a private (or internal) IP address. All devices connected to the same internal network share one private IP address, enabling communication between them only within that network and preventing them from connecting to the public Internet. Although only devices connected to the local network can see these IP addresses, they can still be traced.
Empowering organizations to become ‘data driven’ enterprises with our Cloud experts.
- Reduced infrastructure costs
- Timely data-driven decisions
What are AWS VPC endpoints?
When we shift our workload to the AWS cloud, we create our own Private Network in the cloud using AWS VPC (Virtual private cloud), and we can deploy our services and applications within that private network. If our devices in that VPC network want to have connectivity to the internet to connect with services outside that VPC network can be achieved with the help of Internet Gateway.
But this type of connectivity through internet gateway is over Public Internet hence is not secure and private.
Is it possible to have a private and secure connection between your private VPC and services outside your private VPC network?
Yes! It is possible with AWS VPC endpoints.
AWS VPC endpoints enable a private and secure connection to services outside your VPC without needing internet or internet gateways.
Types of VPC endpoints
There are two types of VPC endpoints.
1. Gateway endpoints – Gateway endpoints provide reliable connectivity to two specific AWS services: AWS S3 and DynamoDB. Gateway endpoints make use of route tables associated with your VPCs. You choose the VPC route tables for the subnets you enable while creating a gateway endpoint. Each routing table you choose immediately includes the next route. The gateway endpoint is the target, and the destination is a prefix list for the service that belongs to AWS.

2. Interface endpoints – Interface endpoints are used to connect with various other services, including AWS S3, but it does not use route tables; instead, it uses AWS Privatelink.
Without VPC endpoints
Access through internet
The following diagram shows that EC2 instances in your Private VPC network can connect to AWS services like S3 and DynamoDB through an internet gateway. But this type of connection is not secure as it traverses through the internet, a public network.
Source:https://docs.aws.amazon.com/images/vpc/latest/privatelink/images/without-gateway-endpoints.png
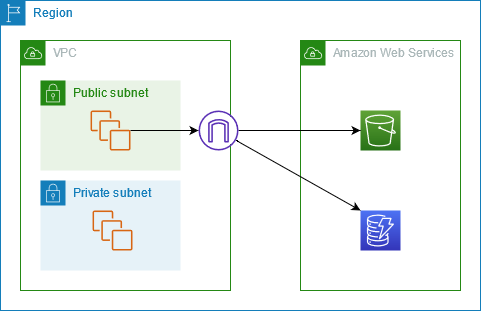
With VPC endpoints
Access through VPC endpoints
This diagram shows that EC2 in the private VPC network connects to S3 and DynamoDB through a gateway endpoint. Request from VPC is routed to the Gateway endpoint. The route table of your VPC should have the entry of destination as service.prefixlist and target as VPC endpoint, which is automatically added at the time of endpoint creation.
This connection is now private traversing through AWS private network without internet and is secure as it is also encrypted.

Source:https://docs.aws.amazon.com/images/vpc/latest/privatelink/images/gateway-endpoints.png
Guide to using VPC endpoints.
Step 1: Create two EC2 instances in your VPC. One in the public subnet and the other in a private subnet, each subnet with its separate route table.
Step 2: Go to VPC endpoints and click on create.

Step 3: Give the desired name in the name tag. In choosing an AWS service, select the gateway endpoint for S3.

Step 4: Under VPC in which you have launched EC2 instances, select the routing table of your EC2 instance in the private subnet.

Step 5: Leave policy and tags as default and click on create endpoints.

Step 6: Observe that the endpoint is created, and the routing table is updated with prefix list entry in the route.


Step 7: SSH into public EC2 through the console. Select the instance and click on connect.

Step 8: Select EC2 instance connect and click on connect.

Step 9: Once inside the EC2 instance, create an empty .pem file using the vi command and paste your EC2 pem key in a new empty file.

Step 10: Change permission of the .pem file using chmod the command to 400 and ssh into private using its private IP address through the following command
ssh – i filename.pem EC2-user@privateipaddress

Step 11: Confirm the internet is not connected by pinging google.com.
Step 12: Configure AWS CLI and try connecting to AWS S3 using the AWS s3 ls command.
![]() Congratulations! You are connected to s3 using VPC endpoints.
Congratulations! You are connected to s3 using VPC endpoints.
Conclusion
AWS VPC endpoints enable a private and secure connection to services outside your private VPC without needing internet or internet gateways. Connectivity through the internet gateway is over Public Internet, hence not secure and private. It is possible with Amazon’s virtual private cloud.
About CloudThat
CloudThat is at the forefront of cloud consulting & training in India with a decade of experience building a solid cloud ecosystem. We have trained 500K+ professionals on various cloud skills, trained 100+ corporates, and accomplished 350+ cloud certifications in 28+ countries. We are Microsoft Gold Partner, AWS Advanced Consulting Partner, Authorized AWS Training Partner, and Authorized VMware Training Reseller.
We deliver all-encompassing consulting services: Cloud Consulting & Migration, Cloud Data Platform, Cloud DevOps & DevSecOps, Cloud Contract Engineering, Cloud Media Services, and Cloud Managed Services.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat
FAQs
1. What are the various VPC endpoint kinds that Amazon VPC offers?
ANS: – Ans: Endpoints of the gateway type are only available for AWS services, such as S3 and DynamoDB. These endpoints will route traffic to the supported services over Amazon’s private network and add an entry to your chosen routing table. Interface-type endpoints provide connectivity over Direct Connect and offer private connectivity to services powered by PrivateLink, whether AWS services, your services, or SaaS solutions.
2. Does communication between instances and an AWS service endpoint across the internet?
ANS: – Ans: The private network of AWS is used for all communication between instances and services hosted there. The packets that come from the AWS network and have an AWS network destination stay on the AWS global network.

WRITTEN BY Aadish Jain


 Login
Login


 March 10, 2023
March 10, 2023 PREV
PREV











Comments