|
Voiced by Amazon Polly |
In today’s digital-first world, managing user identities securely is critical. Whether it’s employees logging into enterprise apps or customers accessing online services, organizations rely on Identity sources and Identity Providers (IdPs) to ensure seamless and secure access. While these terms are often used interchangeably, they serve distinct roles. Let’s break them down.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
What is an Identity Source?
- Definition: The repository where user identity data (username, password, attributes, roles) is stored.
- Examples:
- Active Directory (AD): Common in enterprises for employee records.
- LDAP Directory: Lightweight directory access protocol used in legacy systems.
- HR Database: Stores employee details like job title, department, and contact info.
- Cloud Directories: Azure AD, Google Workspace.
Think of the Identity Source as the “database of truth” for user identities.
What is an Identity Provider (IdP)?
- Definition: A service that authenticates users against the identity source and issues tokens/credentials to applications.
- Examples:
- Okta, Ping Identity, Auth0 – popular SaaS IdPs.
- Microsoft Entra ID (formerly Azure AD) – integrates with multiple sources.
- Google Identity Platform – used for consumer-facing apps.
The IdP acts as the “gatekeeper”, validating credentials and vouching for users.
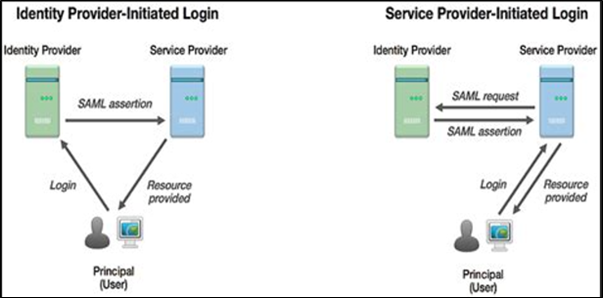
Fig 1: Understanding of Identity Source and Identity Provider
Real-Time Example
Imagine you’re logging into Salesforce at work:
- Your Identity Source is the company’s Active Directory, storing your username and password.
- The Identity Provider (say, Okta) checks your credentials against AD.
- If valid, Okta issues a SAML/OAuth token to Salesforce.
- You’re logged in without re-entering your password, thanks to Single Sign-On (SSO).
Simple diagram to illustrate the flow:
[ User ] → [ Identity Provider (IdP) ] → [ Identity Source (AD/DB) ]
↘ Issues Token ↙
[ Application (e.g., Salesforce) ]
Why It Matters
- Security: Centralized authentication reduces password sprawl.
- Convenience: Enables SSO across multiple apps.
- Scalability: Cloud IdPs integrate with multiple sources and apps.
Note – It is also important to note that Modern Authentication Protocols are used by Identity Providers.
Entra ID (Azure Active Directory / Microsoft Entra ID)
- OAuth 2.0 & OpenID Connect (OIDC): Core standards for app authentication and user identity. OIDC adds the ID token to OAuth 2.0 flows.
- SAML 2.0: Widely used in enterprise single sign-on (SSO) scenarios.
- WS‑Fed: Supports legacy apps via Web Services Federation.
- Passwordless & FIDO2/WebAuthn: Modern phishing-resistant methods supported by Microsoft Authenticator and hardware keys.
- Conditional Access + MFA: Combines contextual policies with multi-factor authentication using TOTP, push notifications, etc.
- Managed Identities: Azure services like VMs and functions authenticate to Azure resources without credentials, leveraging OIDC tokens tied to Entra ID.
- Kerberos / NTLM: For on-prem or Hybrid environments via Azure AD Domain Services.
- OAuth 2.0: Central to accessing Google APIs, supporting various flows:
- Authorization Code (web apps)
- Implicit (client‑side)
- PKCE (SPAs and mobile)
- Service Accounts (server‑to‑server)
- OpenID Connect (OIDC): Built atop OAuth 2.0 for user authentication (Sign In with Google), returning ID tokens.
- Facebook Login (OAuth 2.0-based):
- Uses OAuth 2.0 flows for client-side and server-side web apps.
- Returns access tokens (and ID tokens in OIDC-style) after user consent.
- Enforces scopes, CSRF-protection, and secure token handling.
- OAuth 2.0: Employed for Member Authentication and API access.
- Supports Authorization Code and Implicit flows.
- Implements scope-based permissions (e.g., r_emailaddress, r_liteprofile).
- Uses access tokens with expiration and refresh token support.
- Follows industry best practices for token security and reuse.
Summary Table
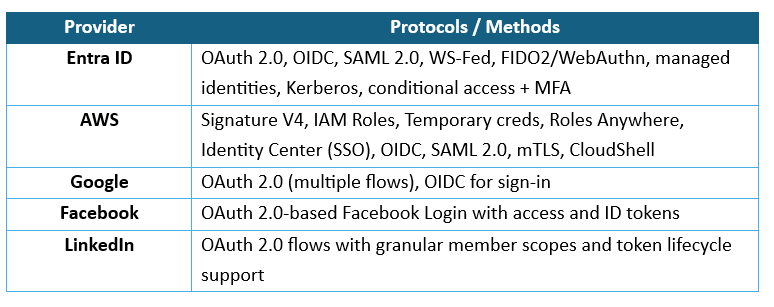
Each provider supports industry standards, including OAuth 2.0 and OIDC, as well as proprietary mechanisms tailored to their ecosystems. AWS extends this with signature-based APIs and certificate-based workflows; Entra ID broadens support into the enterprise and passwordless world, while Facebook and LinkedIn offer OAuth-centric login solutions.
Identity Architecture Explained
Understanding the distinction between Identity Source and Identity Provider is crucial for IT leaders, developers, and security professionals. The source is where identities live, while the provider is the entity that validates them. Together, they form the backbone of modern identity and access management (IAM).
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Amit
Amit Abhay is a Subject Matter Expert at CloudThat, specializing in Microsoft and VMware technologies. With over 15+ years of experience in the IT training domain, he has trained more than 1500+ professionals to upskill in areas such as Microsoft 365 Administration, Modern Device Management and Compliance, VMware Data Centre Virtualization. Known for simplifying complex concepts and delivering hands-on, impactful training, he brings deep technical knowledge and practical application into every learning experience. Amit's passion for continuous learning and emerging technologies reflects in his unique approach to learning and development


 Login
Login


 March 25, 2026
March 25, 2026 PREV
PREV











Comments