In the time when there is a lot of focus on Infrastructure and Operations automation, won’t it be amazing if I say the whole Infrastructure you need can be deployed by just defining a piece of code? Tools like CloudFormation on AWS and Terraform are major players in the Infrastructure as a Code space. But which of these tools suit your requirement and which is the best among them? By end of this post you would be able to infer answers to this question or would be able to get enough pointers to continue your research.
Terraform is a tool by HashiCorp used for building, changing and versioning infrastructure. Before starting the execution, Terraform generates an execution plan elaborating what actions it will take to reach the goal. The whole infrastructure is controlled by Command-line Interface. Terraform can generate and execute incremental plans to update the existing infrastructure to newly described state. In .tfstate the whole infrastructure is defined as JSON that can be easily used for documenting the infrastructure. The infrastructure managed by Terraform are compute instances, storage and networking, DNS and many more.
Why Terraform will be a tycoon of the IaC tool market?
- If we use CloudFormation, then the impact will be restricted to AWS only. People working with multi-cloud need to define and redefine for each cloud provider, but if we use Terraform we can define it once and use across multiple cloud providers. Therefore, we can say that Terraform is one stop solution for IaC tool.
- Configuration tools like Puppet and Chef, install and manage software on existing servers, whereas Terraform has a different way of dealing, it provisions the server itself.
- Other tools can mutate the whole infrastructure resulting in breakage of the services running on it. Suppose, you make a change of version of a software on a node, then it starts producing a different changelog over a span of time, whereas in Terraform this issue does not take place.
- The rollback mechanism of Terraform works in this manner; if a resource is created and fails provisioning, Terraform marks the resource as “tainted” and in the next execution plan, it will remove the tainted resources and execute again unlike CloudFormation rolling back completely.
- In CloudFormation, when we want to launch more instances we need to write the definition for each instance, whereas in Terraform this is not the case i.e. all we need to mention is the number of instances required.
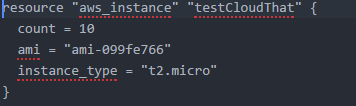
This launches 10 ec2 instances.
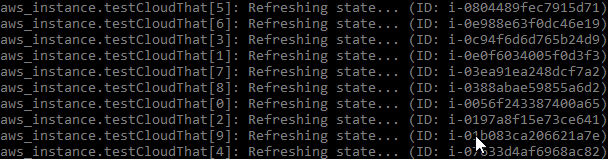
But, when we change it to 3 (we specify only what is our requirement, need not calculate) instances, it kills 7 instances.

And the instances get destroyed (it kills last 7 instances) and 3 remains, unlike other tools
What is so cool about Terraform?
- We can write the desired code either in a txt format or JSON format. If the code is supposed to run programmatically, then it is recommended to use JSON format.
- You can visualize the plan before you execute. This may be helpful in eliminating the undesired steps (catching up bugs). If we run “Terraform plan”, we can visualize our plan like the below image:

- You can generate graph for all your resources that are in use which will give an easy idea about the architecture of the infrastructure you are working in, that too by just adding a simple command “$Terraform graph | dot -Tpng > graph.png”. Here is an example how the graph will look:

This will ease your knowing about the dependencies too and this will also help in applying changes to the infrastructure.
- Suppose, you plan to make few changes and you write the changelog.tf accordingly, then all you need to do is run it by giving the command “Terraform apply” and changes will take place. How Terraform maps the changes to which resource? All this is taken care by Terraform state when we give the command “Terraform apply”. It also builds a file named “terafform.tfstate”. This file contains a custom JSON format that records a mapping from our definition to the actual one.

- When you use Terraform you need not bother to write the Terraform template twice i.e. once in Development and again in Production. All you need to do is define this Template module once and run anywhere by just calling the module.
- When you want to abort your entire infrastructure, all you need to do is give a command “Terraform destroy”. This will terminate all your created resources and you need not worry about manually terminating them.

“All that glitters is not gold”. With so many advantages Terraform also has certain shortcomings with it.
- Firstly, Terraform has no automatic rollback like CloudFormation. So, at the time of need we need to manually find out what went wrong or we need to rollback to the previous version of the code and re-deploy.
- Secondly, whenever Terraform apply takes place it just compares the .tfstate and .tf files and creates the resources which are not present. If .tfstate file is deleted, then it will recreate the resources, so constantly sharing of this .tfstate file is required.
- Thirdly, it does not support conditional statements and looping, therefore we use tricks to overcome it. In the above example, when we launched similar kind of instances we mentioned the number of instance as count = “value”.
Seems as far as ease of accessibility is concerned, Terraform has won the battle over CloudFormation.
I hope this article gave you some weighted pointers to opt for the best IaC tool for your infrastructure. Please feel free to post your views in the comment section below, I will be happy to discuss.
To know more about our training services, visit www.cloudthat.in and for consulting services, visit www.cloudthat.com
WRITTEN BY CloudThat
CloudThat is a leading provider of cloud training and consulting services, empowering individuals and organizations to leverage the full potential of cloud computing. With a commitment to delivering cutting-edge expertise, CloudThat equips professionals with the skills needed to thrive in the digital era.




Amit Gupta
Nov 13, 2017
Nicely compared…Thanks for the write up.
Sandeep
Oct 19, 2017
Awesome article to understand the basic differences !