- Consulting
- Training
- Partners
- About Us
x
Before we understand the implementation of the Azure firewall service, we need to have some idea about traditional Firewalls that are used in corporate data center setup. Enterprise organizations use Firewalls to protect their private resources from malicious attacks from the internet with the help of a set of defined firewall rules.
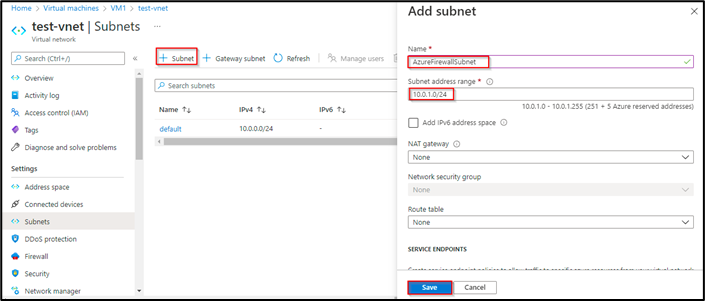
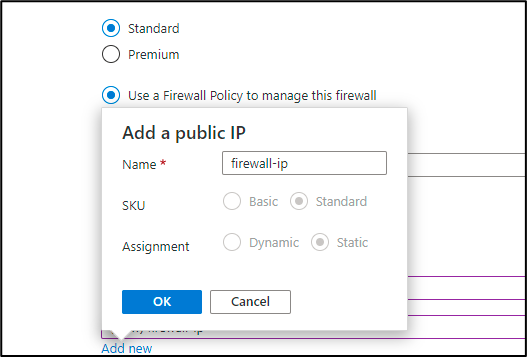
This article will walk you through the steps to configure the Azure Firewall service and set up different firewall rules.
Azure Firewall is a managed service of Azure that has built-in high availability and is stateful, so it understands what packet of traffic/data to allow and what to not. It also has built-in threat intelligence, allowing us to deny traffic from/to malicious IP addresses and domains. We can also deploy an Azure firewall across two or more AZ to ensure high availability. We can also filter traffic based on fully-qualified domain names.




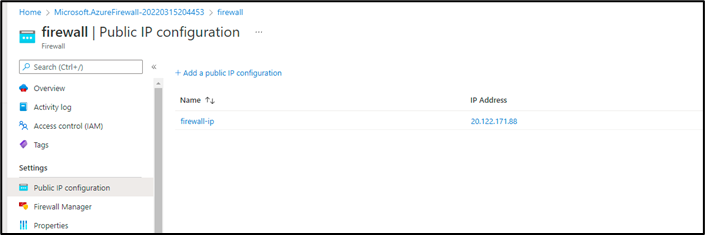






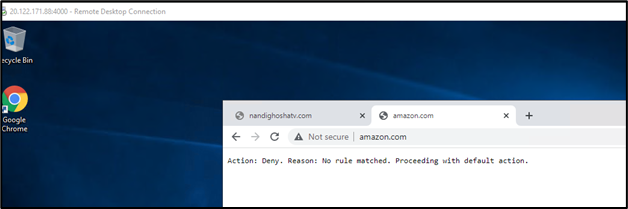
So, we have seen the setup of the Firewall and its different rules and functionalities of it. Still, one of the important points to note when we deploy the Azure Firewall in a virtual network is that we need to deploy the Firewall in the same region as that of the virtual network. It needs to be in the same resource group as the virtual network.
CloudThat is the authorized AWS Well-Architected Partner, helping other businesses build secure, high-performing, resilient, and efficient infrastructures for their application and workloads.
CloudThat is also the official AWS (Amazon Web Services) Advanced Consulting Partner and Training partner and Microsoft gold partner, helping people develop knowledge of the cloud and help their businesses aim for higher goals using best in industry cloud computing practices and expertise. We are on a mission to build a robust cloud computing ecosystem by disseminating knowledge on technological intricacies within the cloud space. Our blogs, webinars, case studies, and white papers enable all the stakeholders in the cloud computing sphere.
Drop a query if you have any questions regarding Microsoft Azure Firewall, Microsoft Azure Services, or consulting opportunities, and I will get back to you quickly. To get started, go through our Expert Advisory page and Managed Services Package that is CloudThat’s offerings.
Yes, Azure Firewall integrates with Azure Monitor to View and analyze firewall logs. We can also send the logs to log analytics and use various tools such as Power BI and Excel to analyze
Azure Firewall is a managed service with built-in high availability and scalability. It is also pre-integrated with certain third-party security providers to provide additional security to our virtual networks.
|
Voiced by Amazon Polly |

CloudThat is a leading provider of cloud training and consulting services, empowering individuals and organizations to leverage the full potential of cloud computing. With a commitment to delivering cutting-edge expertise, CloudThat equips professionals with the skills needed to thrive in the digital era.
Our support doesn't end here. We have monthly newsletters, study guides, practice questions, and more to assist you in upgrading your cloud career. Subscribe to get them all!
Ananay Ojha
Jul 20, 2022
Very Well Written, please keep writing such informative blog.
Kudos to Cloudthat for having such knowledgeable staff. Keep up the good work guys.
Vishal Kalwapalli
May 15, 2022
Thanks
Guruprasad
May 15, 2022
Very informative keep it up Vishal!!!