|
Voiced by Amazon Polly |
Overview
CloudAnix is a cloud-native security platform that provides continuous visibility, compliance monitoring, and threat detection across modern cloud environments. As organizations increasingly adopt multi-cloud infrastructures and containerized workloads, maintaining a strong security posture becomes challenging. CloudAnix helps organizations identify misconfigurations, detect vulnerabilities, enforce compliance standards, and respond to threats in real time.
By integrating directly with cloud providers like AWS, Azure, and GCP, CloudAnix enables teams to monitor and manage security risks while maintaining operational efficiency centrally. Automated remediation, compliance reporting, and actionable insights help DevOps and security teams maintain a strong cloud security posture.
Pioneers in Cloud Consulting & Migration Services
- Reduced infrastructural costs
- Accelerated application deployment
Introduction to CloudAnix
Modern cloud infrastructures are dynamic and highly distributed. Applications run across multiple services such as compute instances, containers, storage services, and serverless functions. While this flexibility accelerates development and scalability, it also introduces new security risks such as misconfigurations, exposed resources, and privilege escalation vulnerabilities.
CloudAnix addresses these challenges by offering a Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platform (CWPP) in a unified platform.
Key capabilities of CloudAnix include:
- Continuous monitoring of cloud environments
- Automated detection of security misconfigurations
- Compliance management for industry standards
- Threat detection and response
- Integration with DevOps and security workflows
This unified approach allows organizations to strengthen their security posture while maintaining agility in cloud operations.
Challenges in Cloud Security Without Centralized Tools
Without a centralized security platform like CloudAnix, organizations often face several operational and security challenges:
- Misconfigured Cloud Resources
Cloud environments often contain misconfigured storage buckets, open ports, or overly permissive IAM policies. These vulnerabilities can expose sensitive data to the internet.
- Lack of Visibility
With multiple cloud services and environments (dev, staging, production), it becomes difficult for security teams to track risks across the entire infrastructure.
- Compliance Complexity
Meeting compliance standards such as SOC 2, CIS Benchmarks, ISO 27001, or PCI-DSS requires continuous monitoring and detailed reporting.
- Slow Incident Response
Manual investigation of security alerts increases response time and may delay mitigation.
- Multi-Cloud Management Difficulties
Organizations using multiple cloud providers must manage security across different tools and dashboards, increasing complexity.
CloudAnix solves these problems by offering centralized visibility, automated security checks, and proactive threat detection.
Architecture and Working of CloudAnix
CloudAnix operates using an agentless architecture, meaning it integrates directly with cloud provider APIs without requiring software installation on individual workloads.
The typical architecture flow includes the following components:
- Cloud Provider Integration
CloudAnix integrates with cloud platforms using secure API access and read-only permissions. For example:
- AWS IAM roles
- Azure service principals
- GCP service accounts
These integrations allow CloudAnix to scan infrastructure resources and collect security data.
- Security Data Collection
Once integrated, CloudAnix continuously collects metadata from cloud services such as:
- Virtual machines
- Containers
- IAM policies
- Storage services
- Network configurations
This information is analyzed for security risks.
- Risk Detection Engine
CloudAnix applies security rules and policies to identify potential threats, such as:
- Publicly exposed resources
- Weak identity permissions
- Outdated packages or vulnerabilities
- Suspicious activities
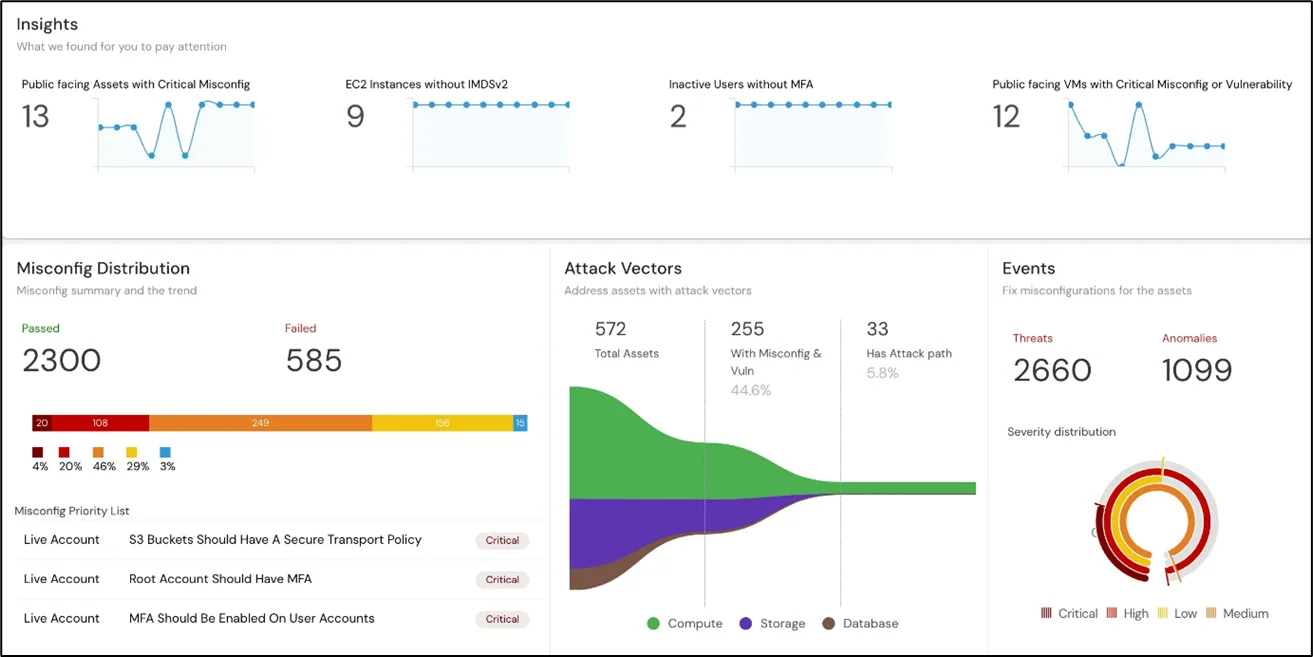
- Dashboard and Reporting
All findings are presented in a centralized dashboard where security teams can:
- View risk scores
- Monitor compliance status
- Investigate vulnerabilities
- Track remediation activities
- Automated Remediation
In some cases, CloudAnix can automatically fix security issues by applying predefined remediation policies.
This architecture allows organizations to continuously monitor and protect their cloud infrastructure without adding operational overhead.
Key Features of CloudAnix
CloudAnix provides several powerful capabilities that help organizations improve cloud security.
- Cloud Security Posture Management (CSPM)
CSPM continuously scans cloud environments to identify misconfigurations and security risks. It ensures that infrastructure follows security best practices.
- Compliance Monitoring
CloudAnix supports compliance frameworks, including:
- CIS Benchmarks
- SOC 2
- ISO 27001
- PCI DSS
Organizations can generate compliance reports and track security controls required for audits.
- Threat Detection
CloudAnix monitors activity logs and system behavior to detect suspicious activity such as unauthorized access attempts or abnormal network traffic.
- Vulnerability Management
The platform scans workloads and identifies vulnerabilities in operating systems, libraries, and applications.
- Identity and Access Monitoring
CloudAnix analyzes IAM policies and permissions to detect overly permissive roles and potential privilege escalation risks.
- Centralized Security Dashboard
The dashboard provides a single view of security posture across all cloud environments, making it easier to identify and prioritize risks.
Integrating CloudAnix with AWS
One common deployment scenario is integrating CloudAnix with AWS environments.
Step 1: Create IAM Role
An IAM role is created in AWS with read-only permissions that allow CloudAnix to access resource metadata.
Step 2: Connect AWS Account
In the CloudAnix console, users provide the required account information and role ARN to establish the integration.
Step 3: Start Security Scanning
After integration, CloudAnix automatically begins scanning the cloud infrastructure for misconfigurations and vulnerabilities.
Step 4: Monitor Findings
Security findings appear in the dashboard, categorized by severity levels such as:
- Critical
- High
- Medium
- Low
Step 5: Remediate Issues
Teams can either manually fix issues or enable automated remediation policies.
Best Practices for Using CloudAnix
To maximize the benefits of CloudAnix, organizations should follow these best practices:
Enable Continuous Monitoring
Ensure CloudAnix is actively scanning all cloud accounts and services to detect issues in real time.
Follow Least Privilege Access
Regularly review IAM permissions and remove unnecessary access rights.
Automate Remediation
Use automated policies to fix common misconfigurations, such as open security groups quickly.
Integrate with DevOps Workflows
Connect CloudAnix alerts with tools like Slack, Jira, or ticketing systems for faster incident response.
Perform Regular Security Reviews
Use the dashboard insights to review the security posture and prioritize risk mitigation periodically.
Conclusion
As organizations continue adopting cloud-native architectures, maintaining a secure cloud environment becomes increasingly complex. CloudAnix provides a comprehensive platform that simplifies cloud security through automated monitoring, compliance management, and threat detection.
Implementing CloudAnix enables businesses to focus on innovation and development while ensuring their cloud infrastructure remains secure and compliant.
Drop a query if you have any questions regarding CloudAnix and we will get back to you quickly.
Making IT Networks Enterprise-ready – Cloud Management Services
- Accelerated cloud migration
- End-to-end view of the cloud environment
About CloudThat
FAQs
1. What is CloudAnix used for?
ANS: – CloudAnix is used for cloud security monitoring, compliance management, vulnerability detection, and automated remediation across cloud environments.
2. Does CloudAnix require agents on servers?
ANS: – No. CloudAnix uses an agentless architecture and integrates directly with cloud provider APIs.
3. Can CloudAnix support multiple cloud providers?
ANS: – Yes. CloudAnix supports multi-cloud environments, including AWS, Azure, and Google Cloud.

WRITTEN BY Akshay Acharya
Akshay Acharya works as a Research Associate at CloudThat. He possesses strong analytical thinking and problem-solving skills, knowledge of AWS cloud services, migration, infrastructure setup, and security, as well as the ability to quickly adopt new technologies and learn.


 Login
Login


 March 12, 2026
March 12, 2026 PREV
PREV











Comments