|
Voiced by Amazon Polly |
Packet Chasing Didn’t Die- It Moved to the Control Plane
Seasoned networking professionals are trained to think in packets:
- Where does traffic originate?
- Which policy touches it next?
- Where can it be dropped?
- What determines its next hop?
In traditional networks, tools like traceroute, tcpdump, and SPAN ports answer those questions. In AWS, packet visibility is abstracted away, but the need for packet-level reasoning remains.
This is where VPC Reachability Analyzer becomes a powerful tool for networking experts. It allows you to mentally chase packets through AWS infrastructure by analyzing the control-plane configuration instead of the data plane.
This blog explains how to use VPC Reachability Analyzer like an expert, aligned with real-world troubleshooting and design workflows.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
What Is VPC Reachability Analyzer?
VPC Reachability Analyzer is a static analysis tool provided by Amazon Web Services that determines whether traffic can flow between two AWS network endpoints.
AWS networking looks complex because it is distributed across multiple control planes.
VPC Reachability Analyzer turns that complexity into deterministic, inspectable logic.
Key properties:
- No live traffic required
- Deterministic results
- Control-plane analysis only
- L3/L4 focused (IP, protocol, port)
It is a A deterministic traceroute + firewall audit across AWS virtual networking
How Networking Experts Should Think About the Tool
The Reachability Analyzer performs the same type of logical evaluation that experienced network engineers do mentally, but faster and at scale. It evaluates routing correctness, analyses policy interactions, identifies both explicit and implicit denies, and verifies path validity across AWS constructs.
However, it does not measure latency, validate application behaviour, or inspect packet payloads.
Because of this, it is particularly well-suited for network design validation, outage root-cause analysis, and pre-change or pre-deployment verification
Mental Model: How AWS “Chases” a Packet
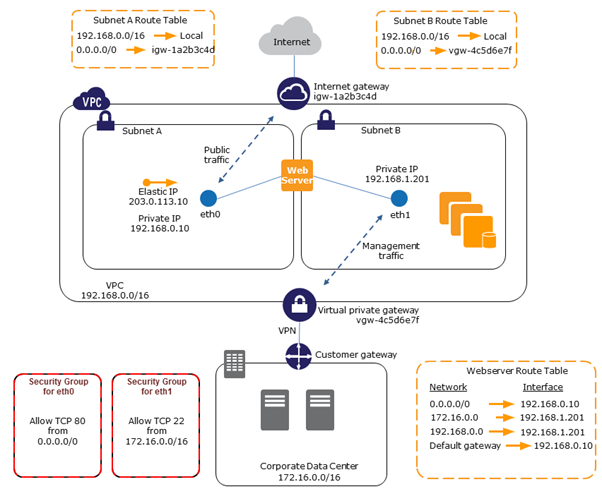
Fig 1: Visual representation of how different devices and components in a network connect and communicate with each other.
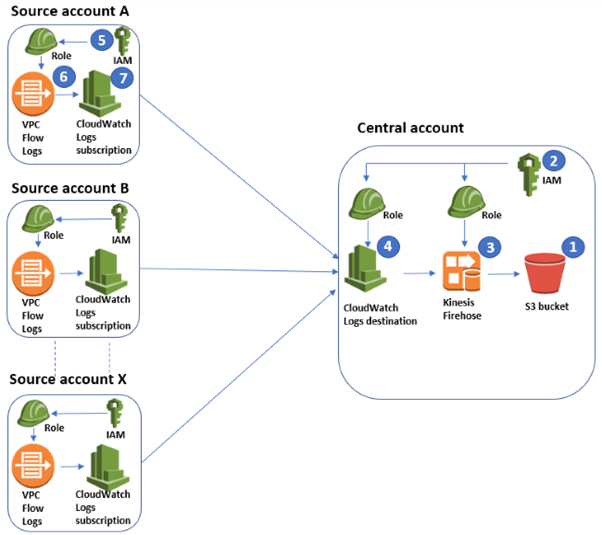
Fig 2: Visual representation of Multi Account Environment.
When an analysis runs, AWS logically evaluates the packet path in this order:
- Source Elastic Network Interface (ENI)
- Outbound Security Group rules
- Source subnet route table
- Routing target
- IGW, NAT Gateway, Transit Gateway, VPC peering, ENI
- Intermediate hops (if any)
- Destination subnet Network ACL (inbound)
- Destination Security Group (inbound)
- Destination ENI
Components That Matter Most with the reachability Analyzer
When using the Reachability Analyzer, understanding the key networking components it evaluates is essential. The tool mirrors how expert engineers think, but knowing what matters most helps you interpret results accurately and avoid common mistakes.
- Elastic Network Interfaces (ENIs)
Every packet in AWS starts and ends at an Elastic Network Interface (ENI). ENIs are the true attachment points of network traffic, not the instances themselves. Multi-homed instances require special attention because traffic may enter or exit through different interfaces. Secondary IP addresses and IP prefixes also play a critical role in determining reachability.
A common source of misanalysis is selecting the wrong ENI as the source or destination. This single mistake often leads to incorrect conclusions about connectivity.
- Security Groups (Stateful)
Security Groups are stateful controls that are evaluated at both the source (egress rules) and the destination (ingress rules). Because they are stateful, return traffic is automatically allowed if the initial request is permitted.
Security Groups do not process rules in order; they function strictly as allow lists. If traffic does not match an allow rule, it is denied by default.
Importantly, routing decisions can never override a Security Group deny. Even if a route exists, traffic will fail if a Security Group blocks it.
- Network ACLs (Stateless)
Network ACLs are stateless and are evaluated before and after routing decisions. Unlike Security Groups, rule order matters, and rules are processed sequentially.
Explicit denies in Network ACLs are a frequent cause of connectivity failures.
One reason experts appreciate Reachability Analyzer is that it highlights the exact rule numbers responsible for allowing or denying traffic, rather than simply stating that access was denied. This level of visibility significantly speeds up troubleshooting.
- Route Tables (Primary Decision Point)
Route tables act as the primary decision point for packet forwarding. AWS uses longest-prefix match logic, meaning the most specific route always wins. Local routes are always evaluated, and routes involving Transit Gateway or VPC peering must exist in both directions for connectivity to succeed.
In practice, most failed reachability analyses stop at the route table layer due to missing, incorrect, or asymmetric routes.
- Transit Gateway: Where Experts Save the Most Time
Transit Gateway is often where complex architectures introduce hidden connectivity gaps. With multiple attachments, route tables, and cross-account connectivity scenarios, troubleshooting manually can be time-consuming. Reachability Analyzer significantly reduces effort by clearly mapping the evaluated path and identifying exactly where traffic stops.
Real-World Expert Scenario
Problem:
An EC2 instance in VPC-A cannot reach an internal service in VPC-B over TCP/443.
Expert workflow:
- Select source ENI
- Select destination ENI
- Specify protocol and port
- Run analysis
Result:
❌ Packet stops at TGW route table
✔ Security groups are correct
✔ NACLs allow traffic
Root cause: Missing return route in destination TGW attachment.
Time saved: Minutes instead of hours.
Traditional Tools
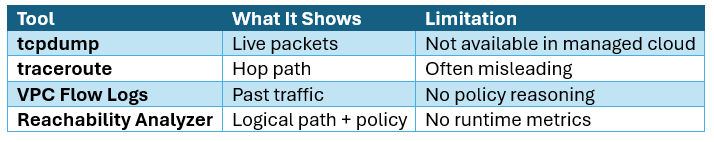
Comparison of network troubleshooting tools and their visibility limitations.
Best Practices for Networking Experts
- Use Reachability Analyzer during architecture reviews
- Validate negative reachability (traffic must NOT flow)
- Run analyses before firewall or routing changes
- Combine with Flow Logs for runtime confirmation
- Teach junior engineers packet logic using analyzer outputs
Packet Chasing, Reimagined for the Cloud
Packet chasing hasn’t disappeared in modern cloud environments; it has evolved. As networking shifts from physical infrastructure to software-defined architectures, tools like VPC Reachability Analyzer redefine how connectivity issues are understood and resolved. By delivering deterministic insights, accelerating root-cause analysis, and increasing confidence in cloud network design, it empowers teams to troubleshoot faster, design better, and operate AWS networks with greater reliability. In a world driven by scale and complexity, this modern approach to packet chasing becomes an essential capability for cloud-first organizations.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Sheeja Narayanan
Sheeja Narayanan is Champion Amazon Authorized Instructor, Microsoft Certified trainer and Senior Subject Matter Expert at CloudThat, specializing in AWS infra and Migration. With 19 years of experience in Training and consulting, she has trained over 2500 professionals/students to upskill in Networking, Windows and Linux administration, AWS, Azure and Vmware. Known for simplifying complex concepts and delivering highly hands-on sessions, she brings deep technical knowledge and practical expertise into every learning experience. Sheeja's passion for training delivery reflects in her unique approach to learning and development.


 Login
Login


 March 16, 2026
March 16, 2026 PREV
PREV











Comments