|
Voiced by Amazon Polly |
Overview
This blog provides an overview of AWS Config and AWS Config Rules, which enable AWS users to maintain compliance with regulatory standards, security policies, and best practices. It also explains when to use managed and custom rules and the importance of testing and monitoring them for better compliance.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
Introduction
AWS Config is a service that provides a detailed inventory of the resources running in your AWS account and a history of configuration changes. AWS Config Rules extends this functionality by enabling you to define rules that evaluate your resource configurations for compliance with best practices, security policies, and regulatory standards.
This blog will discuss the best practices for using AWS Config Rules effectively.
Compliance
Define a clear set of compliance requirements. Before creating Config Rules, defining a clear set of compliance requirements your resources must meet is important. This will help you to create rules that are specific and effective.
To define your compliance requirements, you need to consider the following:
- Regulatory compliance: If your organization is subject to specific regulatory requirements, such as PCI DSS, HIPAA, or GDPR, you need to ensure that your resources are compliant with these standards.
- Security policies: Your organization may have specific security policies that dictate how your resources should be configured. For example, you may require all data to be encrypted in transit and at rest.
- Best practices: AWS provides a set of best practices to use as a guideline for configuring your resources. These best practices cover topics such as security, reliability, and performance.
- Once you have defined your compliance requirements, you can start creating Config Rules that evaluate your resources for compliance.
Use managed rules wherever possible
AWS provides several pre-defined Config Rules covering many common compliance requirements. AWS designed and maintained these managed rules and automatically updated them to reflect changes in best practices and security policies.
Using managed rules can save you time and effort in defining and maintaining your own rules. AWS provides a list of managed rules you can browse and enable for your account.
AWS Config managed rules categories
- Evaluation mode
- Trigger type
- Region Availability
Evaluation mode
There are two types of evaluation modes one is Proactive evaluation, and the other one is Detective evaluation.
- Proactive evaluation: Proactive rules enable the proactive evaluation mode for undeployed resources, enabling you to assess the compliance status of a set of resource properties if they were used to create an AWS resource. This mode determines whether these resources would be considered COMPLIANT or NON_COMPLIANT based on the proactive rules in your account for your Region.

- Detective evaluation: Detective rules are designed to facilitate the detective evaluation mode for already deployed resources, enabling you to assess the configuration settings of your existing resources. This mode allows you to evaluate whether these resources comply with your defined rules.

Trigger type
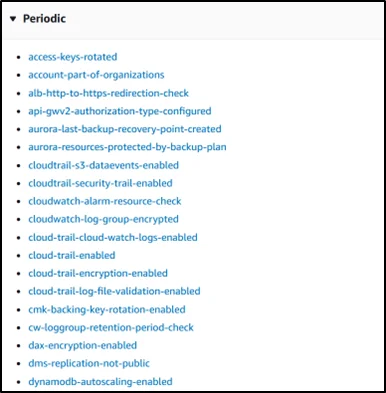
There are three trigger types for AWS Config managed: Periodic, Configuration change, and Hybrid.
- Periodic: Periodic rules are evaluated periodically at a specified frequency, like 12 or 24 hours.
- Configuration change: These rules are evaluated when a Configuration change happens to the resources.

- Hybrid rules: These are evaluated in response to the configuration change and periodic frequency.

The availability of rules differs based on the region also.
Managed rules cover a wide range of compliance requirements, including:
- Security: Managed rules can evaluate your resources for security best practices, such as ensuring that your EC2 instances are running with the latest security patches and that your security groups are configured correctly.
- Cost optimization: Managed rules can help you optimize costs by identifying over-provisioned or underutilized resources.
- Compliance: Managed rules can evaluate your resources for compliance with regulatory standards, such as ensuring that your S3 buckets are encrypted and that your IAM policies are configured correctly.
Use custom rules for specific requirements
While managed rules cover many common compliance requirements, specific requirements may be unique to your organization. In these cases, you can create custom rules tailored to your needs.
To create custom rules, you need to define the following:
- Rule trigger: The event that triggers the evaluation of your rule. This can be a configuration change for resource creation or a resource deletion.
- Rule scope: The resources that your rule applies to. You can define your rule to apply to all or a specific set of resources.
- Rule evaluation: The evaluation logic for your rule. This can be a simple check, such as ensuring that a specific tag is applied to a resource, or a more complex check, such as ensuring that all traffic to and from an EC2 instance is encrypted.
- Rule remediation: The action to take when a resource is non-compliant. This can be an automated action, such as terminating the non-compliant resource, or a manual action, such as sending an alert to an administrator.
Test your rules before deploying them
Before deploying your Config Rules, it’s important to test them thoroughly to ensure they are effective and accurate. This can be done using the AWS Config console, the AWS CLI, or the AWS SDKs.
Testing your rules can help you identify any errors or inconsistencies in your rule logic and ensure that your rules are not generating false positives.
To test your rules, you can create a test resource that is intentionally non-compliant and then evaluate your rule against this resource. You can refine your rule logic until it accurately identifies the non-compliant resource.
Monitor your rules for compliance
Once your Config Rules are deployed, monitoring them regularly is important to ensure they effectively identify non-compliant resources. The AWS Config dashboard can monitor your resources’ compliance status and view detailed compliance reports.
In addition to monitoring your Config Rules, you can configure notifications to alert you when a non-compliant resource is detected. This can be done using Amazon SNS, AWS CloudWatch Events, or AWS Lambda.
Maintain and update your rules regularly
As your infrastructure and compliance requirements evolve, updating and maintaining your Config Rules regularly is important. This can involve updating your rule logic to reflect best practices or regulatory standards changes and adding new rules to cover new resources or compliance requirements.
To maintain and update your Config Rules effectively, you can use versioning to track changes over time. This can help you identify when a rule was last updated and revert to previous versions of your rules if needed.
Pricing
AWS Config
For every configuration change or relationship alteration of a resource, whether an AWS, third-party, or custom resource, a configuration item is recorded in your AWS account per AWS Region. The cost of recording each configuration item is $0.003. The relationship of a resource describes how it is connected to other resources in the AWS account.
AWS Config rules
Your AWS Config charges are based on the number of AWS Config rule evaluations recorded. A rule evaluation is recorded every time a resource is evaluated for compliance against an AWS Config rule. If available, rule evaluations can be executed in detective and/or proactive modes. If you run a rule in both modes, you will only be charged for the evaluations performed in detective mode. The prices are as follows.

Conclusion
AWS Config Rules are a powerful tool for ensuring compliance and best practices in your AWS infrastructure. By defining a clear set of compliance requirements, using managed rules wherever possible, creating custom rules for specific requirements, testing your rules before deploying them, monitoring your compliance rules, and maintaining and updating your rules regularly, you can effectively use Config Rules to ensure that your infrastructure is always compliant and secure.
Remember to follow these best practices to get the most out of your AWS Config Rules implementation. With the right approach, you can ensure that your AWS infrastructure is always compliant and secure and that you can easily identify and remediate any non-compliant resources.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat
FAQs
1. What are the possible evaluation results for an AWS Config rule?
ANS: – COMPLIANT – The rule passes the conditions of the compliance check. NON_COMPLIANT – The rule fails the conditions of the compliance check. ERROR – One of the required/optional parameters is not valid, not of the correct type, or is formatted incorrectly. NOT_APPLICABLE – Used to filter out resources to which the rule’s logic cannot be applied. For example, the alb-desync-mode-check rule only checks Application Load Balancers and ignores Network Load Balancers and Gateway Load Balancers.
2. What are the trigger types for a Config rule?
ANS: – Configuration changes: AWS Config runs evaluations for the rule when there is a resource that matches the rule’s scope and there is a change in the configuration of the resource. Periodic: AWS Config runs evaluations for the rule at a frequency you choose; for example, every 24 hours. Hybrid: Some rules have both configuration changes and periodic triggers. For these rules, AWS Config evaluates your resources when it detects a configuration change and the frequency you specify.

WRITTEN BY Arvind Kishore


 Login
Login


 April 20, 2023
April 20, 2023 PREV
PREV










Comments