|
Voiced by Amazon Polly |
Introduction
AWS Network Firewall is the recently launched, fully managed, highly available, and scalable managed network by AWS, providing security for the VPC’s workloads. AWS Network Firewall works together with AWS Firewall Manager so you can build policies based on AWS Network Firewall rules and then centrally apply those policies across your VPCs and accounts. In the previous blog, we learned about detailed Manual Provisioning of AWS Network Firewall.
Today, we will automate the Provisioning of AWS Network Firewall using Infrastructure as a code DevOps Tool, i.e., Terraform.
Advantages of Terraform:
- Terraform is an open-source Infrastructure-as-Code (IaC) software tool that enables us to create, update and improve Infrastructure in many Cloud Platforms like AWS, Azure, and GCP.
- Terraform Support Reuse of the code.
- We can Provision many numbers physical resources with a single command.
- Terraform has Idempotent property. That is, the state of the infrastructure is saved in local machines. The second application results in 0 changes.
Learn more about Continuous Integration to Automate Terraform modules with GitHub Action as IaC Pipelines here.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
Prerequisites
- Any Linux instances
- AWS root account
- Terraform should be Preinstalled in the Linux machine
- AWS CLI
AWS Services Used
- AWS Network Firewall
- AWS Network Firewall policy
- AWS Network Firewall Rule Groups
- VPC
- Subnets
- Route Table
- Internet Gateway
- Windows instance
Deployment Architecture

Step by Step Guide to Execute the Terraform Code
We are going to Construct the Terraform code in the Linux machine in Modular Format then we execute the code using Terraform Commands.
Step 1: Go to a Linux Instance and connect to an AWS account using AWS CLI.
Step 2: Create a Folder called “NetworkFirewall” and go into the folder.

Step 3: Type Git init to initiate the Git repo to pull the code from GitHub.
Go to NetworkFirewall Folder
|
1 2 3 |
$ git init $ git pull https://github.com/v-karthik-kumar/FirewallTerraform.git |
Step 4: Go to FirewallTerraform Folder
|
1 |
$ cd FirewallTerraform |

Step 5: Here you can see the Files Folders.
File Main.tf
The use of main.tf file is used to put the code in Modular format.
Run the Below Code to see the code.
|
1 |
$cat main.tf |

File Var.tf
This File contains all the variables declared in the Terraform Code. The code Reusability is achieved here. If we change the values in the variable. We can use the same code to provision similar infrastructure.

File Provider.tf – This File contains the CloudProvider details.

Step 6: Now Go into the module Folder by running the below code.
|
1 |
$cd module |
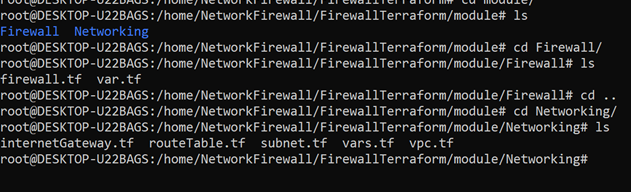
Here you will see two folders, Firewall, and Networking. Here we are segregating the Resource to the provision in the AWS platform in a modular way. Go into each folder and check the Files present.
Step 7: Now Go back to the Folder where main.tf File is presently using the below command.
|
1 |
$ cd /home/NetworkFirewall/FirewallTerraform |
Execute the below Code
Initialize the terraform code.
|
1 |
$ terraform init |
Output: If no errors.

Execute the below code to preview the action Terraform would take to modify your Infrastructure.
|
1 |
$ terraform plan |
Output: If not Errors.

Execute the below Code:
The terraform apply command performs a plan just like terraform plan does, but then actually carries out the planned changes to each resource using the relevant infrastructure provider’s API.
|
1 |
$ terraform apply --auto-approve |

You will get the output in this way. Provisioning AWS Network Firewall using terraform started.
Step 8: Check and verify the newly provisioned resources in the AWS console.
VPC

Subnets

Route Table

Internet Gateway

Firewall

Firewall Policy

Firewall Rule Group

Step 9: Create an windows instance in Firewall-VPC in Resource subnet. Try to access the blocked domain name in the browser. You will find error page or page not found.

Step 10: Destroy the Infrastructure using the below command.
|
1 |
$ terraform destroy –auto-approve |
If you get any errors, Try again the same command.
Conclusion
Provisioning infrastructure on the cloud using Terraform gives us more grip on the infrastructure and fewer manual tasks. The configuration language is human-readable, making us write the infra code more quickly. This allows us to track resource changes or any updates throughout the deployment.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat
FAQs
1. What is the importance of making modules in the terraform?
ANS: – Using modules we can create multiple and smaller terraform files. Which altogether makes a big terraform script. Updating and editing the code would become simpler and easier. We will be getting the possibility to Reuse the Code in many deployments.
2. What are the capabilities, in terms of security for the services and workloads in AWS?
ANS: – We have a few services like Security Groups, which provide security for the instance level. Network Control List, which provides the security for the Subnet level. AWS WAF provides the security for the workload or applications that are running on the CloudFront, load balancers, and API. AWS shield provides security against DDoS attacks.

WRITTEN BY Karthik Kumar P V
Karthik Kumar Patro Voona is a Research Associate (Kubernetes) at CloudThat Technologies. He Holds Bachelor's degree in Information and Technology and has good programming knowledge of Python. He has experience in both AWS and Azure. He has a passion for Cloud-computing and DevOps. He has good working experience in Kubernetes and DevOps Tools like Terraform, Ansible, and Jenkins. He is a very good Team player, Adaptive and interested in exploring new technologies.


 Login
Login


 September 22, 2022
September 22, 2022 PREV
PREV











Comments