|
Voiced by Amazon Polly |
Microsoft Defender for Identity is a cloud-based security solution that monitors Active Directory signals to detect credential theft, lateral movement, and privilege escalation attacks in hybrid environments.
As identity becomes the primary attack surface in modern enterprises, organizations must prioritize identity threat detection alongside endpoint and network protection. Microsoft Defender for Identity provides deep visibility into authentication behaviour and domain controller activity, helping security teams detect sophisticated attacks early and reduce exposure to risk.
Start Learning In-Demand Tech Skills with Expert-Led Training
- Industry-Authorized Curriculum
- Expert-led Training
Why Identity Threat Detection Is Critical
Most modern breaches begin with compromised credentials. Once attackers gain access, they attempt to escalate privileges, move laterally, and establish persistence within the environment.
Microsoft Defender for Identity continuously analyzes authentication patterns, directory queries, and privileged account activity to detect abnormal behaviors associated with real-world attack techniques. By focusing on identity infrastructure, organizations can reduce attacker dwell time and prevent domain-wide compromise.
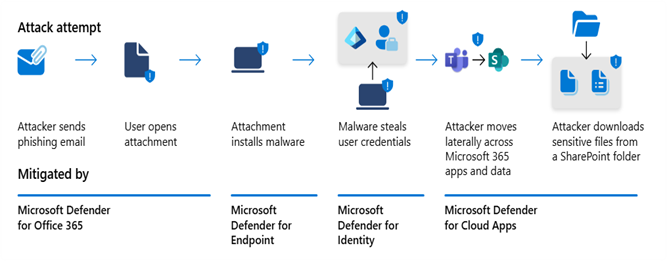
Fig 1: Attack lifecycle diagram – From credential compromise to lateral movement
Unified Security Through Integrated Detection
Identity threats rarely occur in isolation. A compromised account may be associated with endpoint activity or suspicious cloud access. Microsoft Defender for Identity integrates with Microsoft Defender XDR, enabling correlated detection across identity, endpoints, cloud apps, and workloads.
This unified visibility allows organizations to:
- Consolidate related alerts into a single incident.
- Understand the complete attack chain.
- Reduce investigation time.
- Improve response prioritization.
Rather than investigating fragmented alerts, security teams gain contextual clarity.
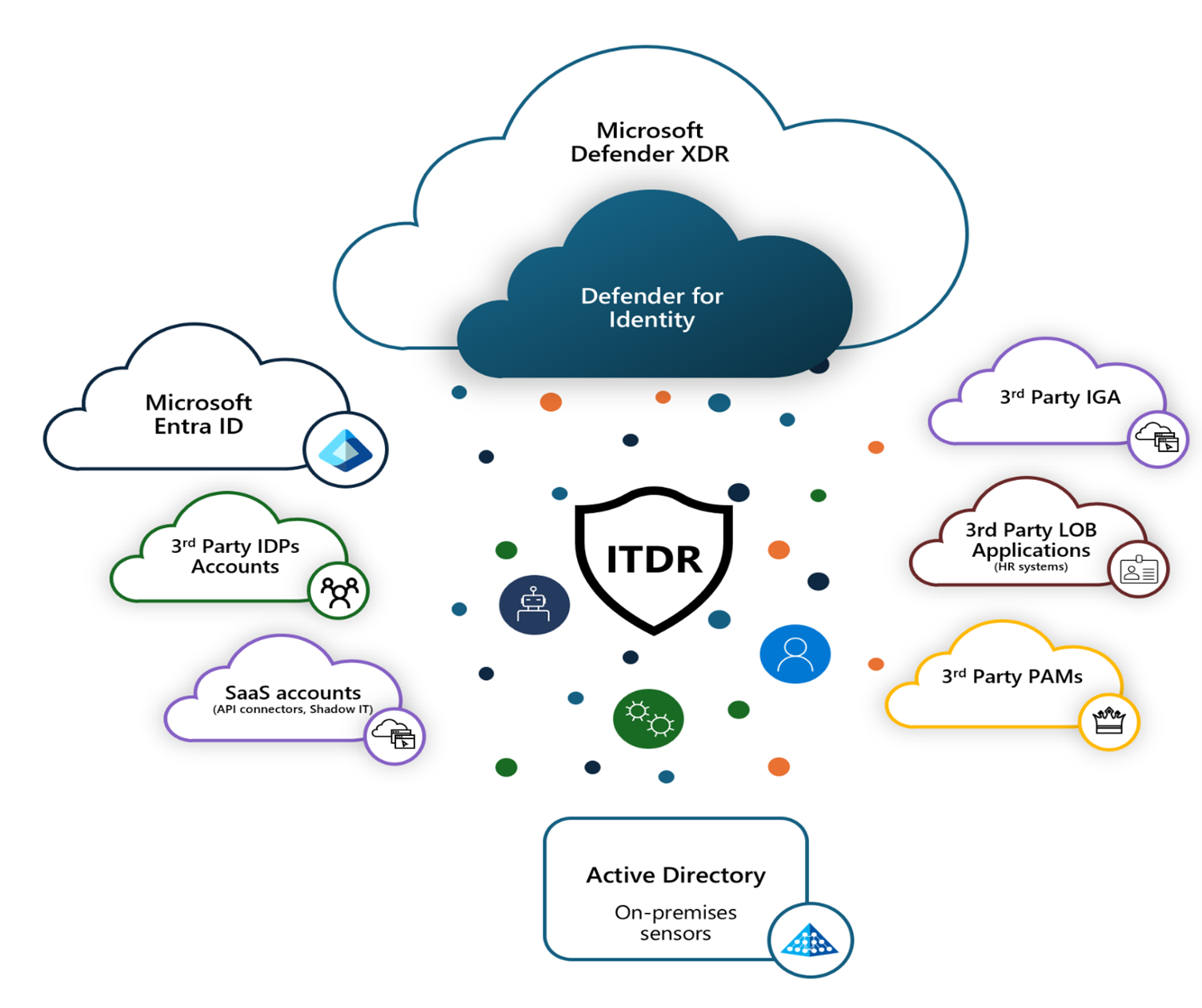 Fig 2: Architecture diagram – Identity signals integrated with Microsoft Defender XDR
Fig 2: Architecture diagram – Identity signals integrated with Microsoft Defender XDR
Hybrid Identity Monitoring Across Environments
Modern enterprises operate hybrid identity models that combine on-premises Active Directory with cloud identity services. Attackers often pivot between these layers to evade detection.
Microsoft Defender for Identity monitors domain controller activity and correlates signals with Microsoft Entra ID, strengthening detection of:
- Privileged account misuse
- Suspicious authentication attempts
- Directory reconnaissance
- Lateral movement behaviors
By securing both on-premises and cloud identity layers, organizations create stronger protection around their most critical security boundary, identity.
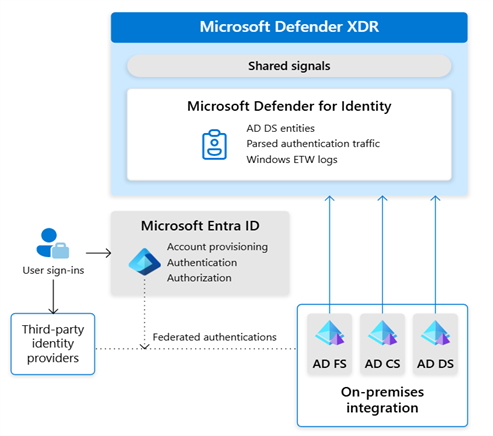
Fig 3: Hybrid identity architecture – Active Directory integrated with Microsoft Entra ID and Defender
Business Impact and Operational Benefits
Beyond technical detection capabilities, Microsoft Defender for Identity delivers measurable business value:
- Reduced risk of credential-based breaches
- Improved compliance and audit readiness
- Faster investigation and remediation
- Stronger protection for privileged accounts
Security professionals responsible for identity protection and threat detection can further enhance their technical proficiency through industry-recognized Microsoft security certifications, which validate expertise in hybrid identity monitoring, advanced threat detection, and enterprise security operations aligned with modern architectural best practices.
Securing Enterprise Identities
As cyberattacks increasingly target authentication systems and privileged accounts, protecting identity infrastructure is no longer optional- it is a strategic necessity. Microsoft Defender for Identity delivers advanced identity threat detection capabilities that help organizations detect credential misuse, identify lateral movement, and prevent privilege escalation before attackers gain full control.
By providing continuous visibility into domain controller activity and correlating identity signals across hybrid environments, organizations can significantly reduce attacker dwell time and improve incident response effectiveness. This proactive detection model not only strengthens technical defences but also enhances compliance posture, audit readiness, and overall operational resilience.
In today’s threat landscape, identity is the central control plane of enterprise security. When identity is secured, access is controlled, risks are minimized, and business continuity is protected.
In modern enterprise security, defending identity ultimately means defending the organization itself.
Upskill Your Teams with Enterprise-Ready Tech Training Programs
- Team-wide Customizable Programs
- Measurable Business Outcomes
About CloudThat

WRITTEN BY Navitha Wilson
Navitha Wilson is a Microsoft Certified Trainer and Subject Matter Expert in Azure Infrastructure and Architecture at CloudThat, with a strong focus on Microsoft Azure and Hybrid Infrastructure. With over 13 years of experience in training and academics, she has empowered 5,000+ professionals and learners through her expertise in Azure Administration, Networking and Security. She is also a Cisco Certified Network Professional (CCNP) in Routing and Switching, with robust hands-on experience across cloud and on-premises environments. Renowned for her ability to simplify complex technical concepts and deliver engaging hands-on sessions, Navitha consistently receives outstanding feedback from learners and is widely recognized as an exceptional trainer. Her training style blends deep technical knowledge with practical application, ensuring impactful and results-driven learning experiences. Navitha’s passion for technology and reading fuels her unique and inspiring approach to learning and development.


 Login
Login


 March 23, 2026
March 23, 2026 PREV
PREV










Comments