|
Voiced by Amazon Polly |
Overview
In the fast-paced world of modern cloud engineering, security and compliance can no longer afford to be an afterthought or a manual bottleneck at the end of a release cycle. This post explores the transition from traditional, manual security gates to Continuous Compliance, introducing the concept of the “Pipeline as a Contract.” We will break down how Policy-as-Code, automated Software Bill of Materials (SBOMs), and cryptographic attestations are turning deployment scripts into auditable, legally enforceable enforcement mechanisms.
Pioneers in Cloud Consulting & Migration Services
- Reduced infrastructural costs
- Accelerated application deployment
Introduction
Not too long ago, deploying to production meant surviving the “Change Advisory Board” (CAB), a slow, manual review process where compliance teams squinted at spreadsheets to ensure security policies were met. Today, that model is entirely broken.
With global data regulations hardening and software supply chain attacks becoming more sophisticated, organizations need absolute certainty about what is running in their environments. You can’t just promise that a container is secure; you have to prove it mathematically.
Enter the era of Continuous Compliance. In 2026, we are no longer treating the CI/CD pipeline as just a glorified script that moves code from Point A to Point B. Instead, the pipeline has evolved into a strict, auditable contract. If the code doesn’t meet the precise legal and security specifications codified in the pipeline, it simply cannot exist in production. The guardrail has replaced the gatekeeper.
The Problem: Why Manual Compliance Fails
In a world where engineering teams deploy multiple times a day across distributed, multi-cloud environments, human-driven compliance checks are impossible to scale.
- The Speed Gap: Security reviews take days; developers merge code in minutes.
- Human Error: Manual audits inevitably miss misconfigurations, like an overly permissive AWS IAM role or an unpatched vulnerability in a deep transitive dependency.
- Audit Nightmares: Proving compliance to external auditors historically required massive archeological digs through Jira tickets and Slack logs.
The Solution: The "Pipeline as a Contract"
Treating the pipeline as a contract means shifting from detecting compliance violations in production to preventing them at the build phase. The pipeline acts as a legally binding checkpoint. It programmatically guarantees that every artifact deployed meets the organization’s exact security posture.
Core Components of a Contractual Pipeline
To build this architecture, engineers are relying on three foundational pillars:
- Policy-as-Code (PaC):
Using tools like Open Policy Agent (OPA) or Kyverno, compliance rules are written in a declarative language (like Rego). Instead of a PDF document stating “No public Amazon S3 buckets,” you have code that automatically blocks any Terraform plan attempting to provision one.
2. The Software Bill of Materials (SBOM):
You can’t secure what you don’t know you have. A modern pipeline automatically generates an SBOM for every build, a comprehensive, machine-readable inventory of the libraries, frameworks, and dependencies used in the application.
3. Cryptographic Attestations:
Tools like Sigstore (Cosign) are used to digitally sign artifacts and attest to the steps they went through. The pipeline generates an attestation proving, “This image was built from this specific commit, scanned by this specific tool, and passed all OPA policies.” The Kubernetes admission controller then verifies this signature before allowing the pod to spin up.
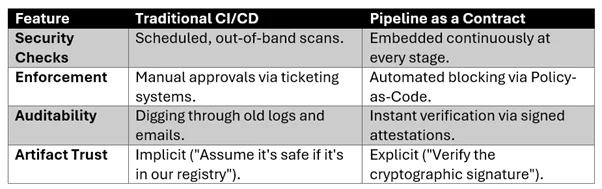
The Old Way vs. The New Way
The Developer Experience (DevEx)
A common fear is that strict compliance slows developers down. Paradoxically, the “Pipeline as a Contract” speeds them up. Because the rules are codified and transparent, developers get instant feedback in their IDEs or via pull request comments. They don’t have to wait three days for a security engineer to reject their ticket; the pipeline tells them exactly what policy they violated in seconds.
Conclusion
You no longer have to choose between deploying fast and deploying securely. When your policies are your code, compliance simply becomes a byproduct of doing your job well.
Drop a query if you have any questions regarding CI/CD pipeline and we will get back to you quickly.
Empowering organizations to become ‘data driven’ enterprises with our Cloud experts.
- Reduced infrastructure costs
- Timely data-driven decisions
About CloudThat
FAQs
1. What exactly is Policy-as-Code?
ANS: – Policy-as-Code is the practice of writing rules and governance conditions in a high-level programming language. These scripts are then executed by an engine (like OPA) to automatically accept or reject infrastructure changes or deployments based on those rules.
2. Does implementing a "Pipeline as a Contract" slow down developer velocity?
ANS: – Initially, there is a learning curve to integrating the tools. However, in the long run, it drastically increases velocity by removing manual security review bottlenecks and providing developers with immediate, actionable feedback when a rule is broken.
3. How does this differ from traditional DevSecOps?
ANS: – Traditional DevSecOps often just meant adding security scanning tools (like SAST/DAST) into a pipeline. Continuous Compliance takes it a step further by cryptographically signing the results of those scans and using Policy-as-Code to enforce hard, auditable boundaries that cannot be bypassed.

WRITTEN BY Shakti Singh Chouhan
Shakti Singh is a Cloud Engineer with over 3.5 years of experience in designing, deploying, and securing scalable AWS infrastructures. A DevOps enthusiast, he is passionate about automation, security, and cloud migration. Shakti enjoys sharing insights on cloud technologies, problem-solving, and fostering a culture of continuous learning.


 Login
Login


 March 23, 2026
March 23, 2026 PREV
PREV










Comments